As companies embrace new network connected platforms and development shifts such as Cloud, mobile, SaaS, and DevOps, they have also expanded the surfaces that need protection from cyber-attacks. We spoke with David Cummins, VP of EMEA, Tenable, the first and only provider of Cyber Exposure solutions, about how they empower organizations across all industries to understand and reduce the risks they face.
This interview was originally published on October 5, 2020.
What is Tenable?
Founded in 2002, Tenable is the first and only provider of Cyber Exposure solutions. We work with more than 30,000 organizations worldwide to help them manage and measure cybersecurity risk in the digital era. We are building on our deep technology expertise as a pioneer in the vulnerability assessment and management market, providing visibility across the modern attack surface and deep insights to help security teams, executives, and boards of directors prioritize and measure Cyber Exposure.
While nation-state attacks and advanced persistent threats might grab headlines, the reality is that these types of attacks aren’t an everyday occurrence. In truth, the majority of intrusions are through well-known vulnerabilities that should have been addressed. By addressing known vulnerabilities being actively exploited by threat actors on all compute platforms, organizations can significantly reduce their cyber exposure.
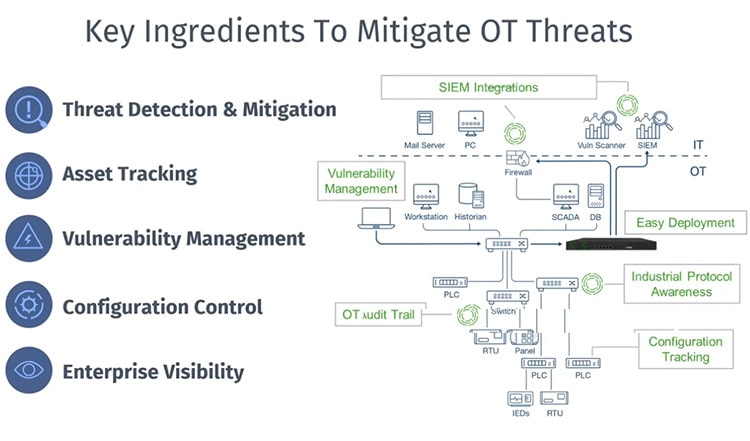
The Tenable Cyber Exposure platform is the industry’s first solution to holistically assess, manage, and measure cyber risk across the modern attack surface. The Tenable platform, underpinned by Nessus, uniquely provides the breadth of visibility into cyber risk across IT, Cloud, IoT, and OT environments and the depth of analytics to measure and communicate cyber risk in business terms for making better strategic decisions. The platform consists of Tenable.sc (managed On-Prem), Tenable.io (managed in the Cloud), and Tenable.ot (to protect industrial environments). Tenable Lumin brings everything together, transforming vulnerability data into meaningful business insights based on cyber risk.
How does Nessus assess vulnerability?
Built for security practitioners by security practitioners, Nessus is the industry’s most accurate, comprehensive, and widely adopted solution for point-in-time vulnerability assessments.
Organizations use Nessus to assess their environment to identify vulnerabilities — including software flaws, missing patches, malware, and misconfigurations — across various operating systems, devices, and applications.
Nessus has the most in-depth and broadest coverage with more than 130,000 plugins, coverage for more than 50,000 CVE, and over 100 new plugins released weekly within 24 hours of vulnerability disclosure.
In addition, Tenable Research works closely with the security community to discover new vulnerabilities (we have found more than 100 zero-day vulnerabilities in the last year alone) and provide insights to help organizations mature their vulnerability assessment practices. We build this intelligence into Nessus through plugins to help take the guesswork out of vulnerability assessment for more accurate, comprehensive vulnerability assessment.
What solutions do you offer for DevOps and application security?
The rapid adoption of DevOps is leaving traditional security practices in the dust. Manual processes, infrequent scans, and siloed tools cannot keep up with the pace of development and continuous release cycles. As a result, DevOps and application development are creating a Cyber Exposure gap that puts some of the most sensitive data and systems in any organization at risk. Cybersecurity leaders must rise to this challenge and find new approaches to securely enable business innovation.
Tenable.io Container Security integrates security before application deployment to secure DevOps processes by providing visibility into the security of container images – including vulnerabilities and policy violations – through integration with the build process. Compatible with the DevOps toolchain that developers already use, Tenable.io Container Security brings proactive visibility and security to solve the security challenges of containers at the speed of DevOps.
Tenable.io Web App Scanning provides easy-to-use, comprehensive, and automated vulnerability scanning for modern web applications. Tenable.io WAS allows you to quickly configure and manage web app scans in a matter of minutes with minimal tuning.
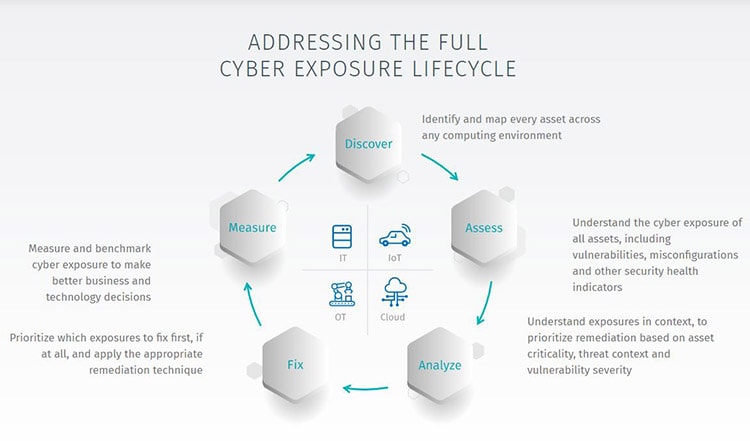
What are your five steps of effective risk-based vulnerability management for Cloud Security?
The core of cloud security is that fundamentally it should be approached in the same way as any other computing platform. Effective risk-based vulnerability management requires a strong process mapped directly to five Cyber Exposure phases:
- Discover – identify and map every asset across all computing environments
- Assess – understand the cyber exposure of all assets, including vulnerabilities, misconfigurations, and other security health indicators
- Prioritize – understand exposures in context to prioritize remediation based on asset criticality, threat context, and vulnerability severity
- Remediate – determine which exposures to fix first and apply the appropriate remediation or mitigation technique
- Measure – calculate, communicate and compare Cyber Exposure and key maturity metrics to drive risk reduction
How can Container Security help reduce cyber risk?
As organizations increasingly depend on software to provide a competitive advantage, the enterprise requirements for secure, rapid, and efficient delivery of software have never been greater. DevOps teams are answering the business requirement for speed and agility by streamlining software delivery processes. Increasingly, they utilize containers to quickly build and stand up new services and applications. Containers, however, present significant security risks. The lack of IP addressability, short-lived lifespans, and sheer volume and variety of containers mean securing them is an ongoing challenge.
Gaining pre-production visibility into containers is critical so that organizations can understand the potential risks in containerized applications before they are deployed. DevOps teams get the information they need to quickly remediate vulnerabilities and malware in containerized images as early in the development process as possible, reducing risk prior to deployment and accelerating development.
What is PCI DSS ASV assessment, and how does your platform help with compliance?
According to the PCI Security Standards website, a PCI DSS ASV assessment is ‘an organization with a set of security services and tools (“ASV scan solution”) to conduct external vulnerability scanning services to validate adherence to external scanning requirements of PCI DSS Requirement 11.2.2.’
Tenable.io PCI ASV, an add-on to Tenable.io, streamlining verification of adherence with the PCI Data Security Standard. With pre-configured scan templates, and an efficient evidence/dispute resolution process, Tenable.io PCI ASV allows organizations to run scans quickly, submit attestation requests and resolve disputes.
Which other types of compliance do you monitor?
Compliance requirements continue to increase, and business partners often require conformance with an accepted security standard, such as ISO 27001/2. That said, adopting a security standard is rarely like buying off-the-shelf clothes from a local retailer. Tenable helps organizations tailor their efforts to meet each specific situation, automate controls, and generate reports.
Providing hardware and software discovery, vulnerability management, and configuration assessment, Tenable enables organizations to implement a single protective control foundation to support multiple compliance requirements and security standards.
Once your solutions identify security risks and vulnerabilities, does it offer recommendations for fixing them?
Tenable helps an organization’s security team focus on the vulnerabilities and assets that matter most, so they can address the true business risk, instead of wasting valuable time on vulnerabilities attackers may not likely exploit.
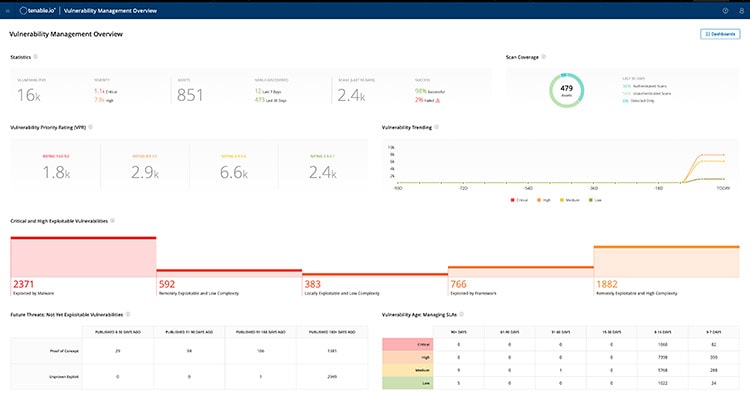
Predictive Prioritization, available as standard in Tenable.io and Tenable.sc, combines Tenable-collected vulnerability data with third-party vulnerability and threat data and analyzes them together with the advanced data science algorithm developed by Tenable Research. Each vulnerability receives a Vulnerability Priority Rating (VPR) that incorporates the result of this analysis, updated daily, including vulnerabilities that have yet to be published in the National Vulnerability Database (NVD).
Tenable also helps enterprises and CISOs prioritize their assets based on indicators of business value and impact to the firm. Unlike VPR, which is an absolute value, the Asset Criticality Rating (ACR) is a subjective measurement, modifiable by the organization. The reason is simple — organizations know their applications and assets best and can determine if a particular component needs more or less attention.
Assessment Maturity in Tenable Lumin translates raw, technical data into actionable steps for improving security program effectiveness. It measures two key dimensions, the frequency, and depth of vulnerability assessments, to identify organizations’ Assessment Maturity Score. This bolsters the existing Vulnerability Priority Rating (VPR) and Asset Criticality Rating (ACR) in Tenable Lumin to provide organizations with an objective measure of their overall cyber risk. Organizations can use these metrics to drive improvements by optimizing security investments and building a business case for foundational controls to reduce risk across the enterprise.
By understanding the full context of each vulnerability, the criticality of affected assets, and an assessment of current and likely future attacker activity, security teams can prioritize efforts to reduce the greatest amount of business risk with the least amount of effort. Remediation scans then validate if vulnerability remediation actions on targets have been successful.
What are some of the ways different industries are utilizing your products?
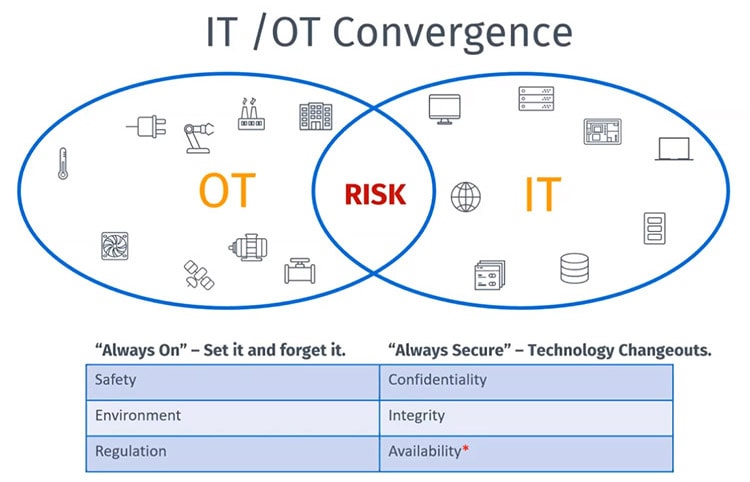
Organizations of all sizes have embraced digital transformation to create new business models and ecosystems, deliver new products and services, and operate more efficiently in the digital economy. New digital computing platforms and development shifts such as Cloud, mobile, SaaS, and DevOps have made it possible to move from concept to capability daily. Physical devices and systems of all types – from corporate conference systems to power grids – are now network connected and programmable, creating even more opportunities for digital transformation, but also hugely expanding the attack surface our customers have to defend.
Tenable empowers all organizations across all industries – from banks and financial services, retail, manufacturing, public sector, transport, utilities, and more, to understand and reduce the risks they face.
How can Tenable users get support?
Tenable is firmly committed to the success of our customers, so we offer personalized deployment and technical support to meet their needs, now and in the future. Our goal is to ensure an outstanding customer experience at every touchpoint. Whether a prospective, new, or established customer, the Tenable Customer Success Team and our certified partners will help attain a successful deployment and accomplish security goals.
Driven by an uncompromising commitment to excellence, our professionals leverage their decades of expertise, knowledge of best practices, and extensive hands-on experience to deliver professional support tailored precisely to the needs of our customers.
Full details of our support plans can be found on our website.