Originally published on December 11th, 2020
Company name and location: Marriage Tax Allowance Ltd, based in the United Kingdom
Leak size: Over 100,000 files totaling approximately 5GB of data
Number of people exposed: >100,000
Data Storage Format: Directory Listing in the form of PDF documents
Countries Affected: United Kingdom
A UK-based company specializing in recovering marriage tax allowance funds for UK clients has suffered a damaging data leak that could have led to the potential dissemination of all its clients’ personal information. It is important to note, however, that it is impossible for us to say whether the specific server vulnerability that led to the leak, actually led to sensitive information falling into the hands of nefarious users.
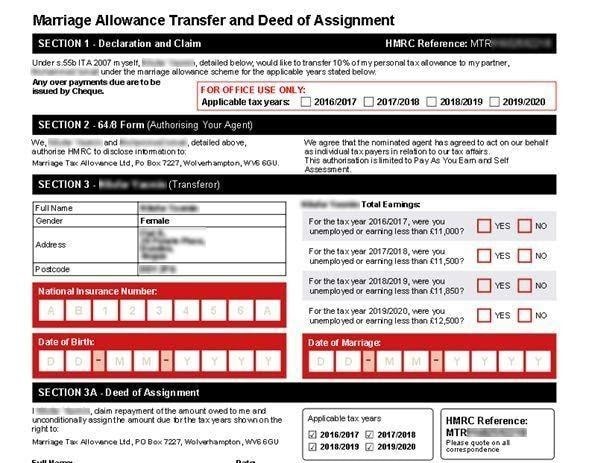
As part of conducting routine server scans for potential vulnerabilities, the Website Planet team discovered that Marriage Tax Allowance Ltd misconfigured its WordPress content management system (CMS), thereby leaving the directory listing enabled for public view. This allowed anyone to browse the entire list of files stored on the website. More specifically, letters to customers, containing customer information, were written to the same directories
The vulnerability meant that anyone attempting to access the company’s directory listing could have done so without encountering basic security measures such as password protection. Accessing the correct URL allowed users to access the full pipedrive database.
Leaked Customer Data
All the exposed data was contained in .PDF files and included Personally Identifiable Information (PII) such as:
- Applicant’s full name
- Applicant’s gender
- Full Home address
- Partner’s full name
- Partner’s gender
- Refund amount customers could request
The lack of adequate security meant the company allowed hundreds of thousands of PDF files showing customers’ personal information to become exposed.
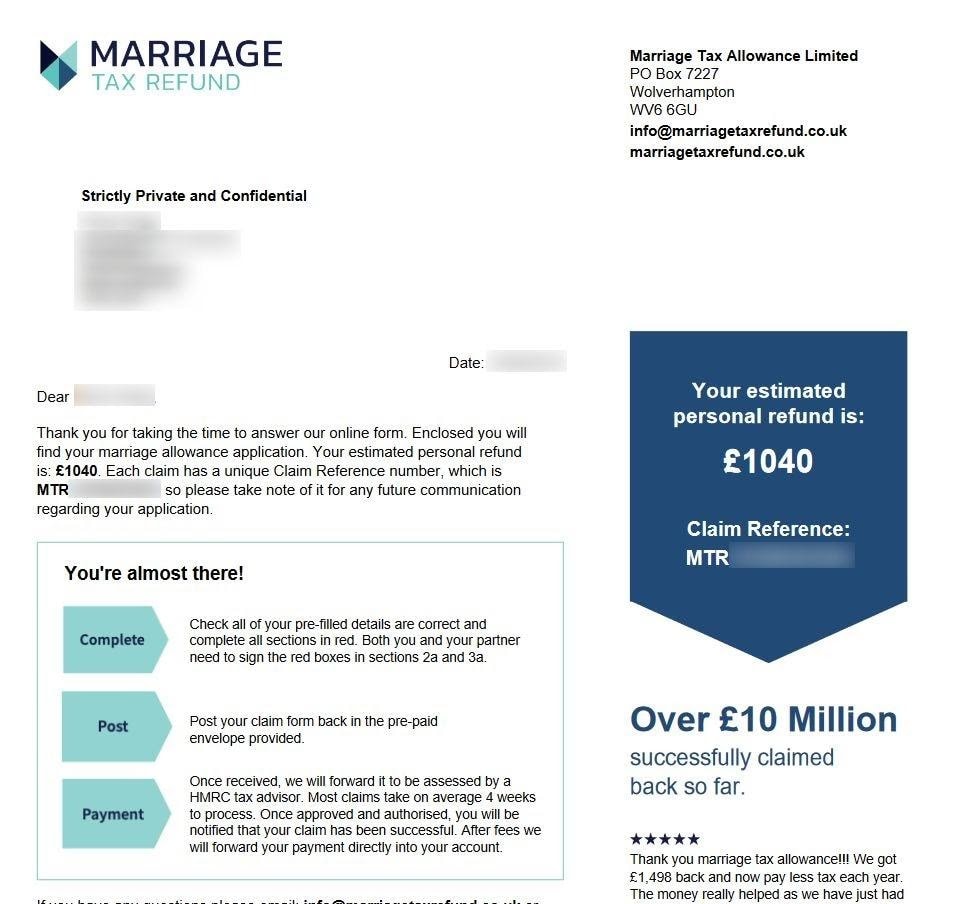
According to our research team, each customer, or couple, had two files associated with them – one document showing each couple’s details and a further “thank you” document, kept on record to inform the applicants that their submission was approved (and that they would be receiving a refund).
Who was affected?
The leak exposed more than 100,000 customers that signed up with Marriage Tax Refund Ltd since the company’s incorporation in October 2016.
Our research team found that Marriage Tax Refund had over 100,000 unsecure PDF files and kept 2 files per couple, meaning that over 100,000 individuals were exposed in the leak.
Currently, it is unknown whether the data leak exposed the entirety of the company’s customer base, or just a batch of 100,000 files.
Who Was Leaking the Data?
Marriage Tax Refund is a registered UK-based company headquartered in Wolverhampton, providing administrative services for married couples seeking tax relief. In exchange for nominating the company as the customer’s legally appointed representative with the UK’s tax bureau (the HMRC), the company charges its customers a minimum fee of $99 + tax in addition to a further 30% + tax fee for every successful claim.
The company claims that over 4.5 million couples in the UK are charged an incorrect amount of tax each year and offers its customers the chance to claim back up to £15,000, with their assistance. According to Marriage Tax Refund, the company helps its customers claim an average of £900 with an estimated lifetime saving of £15,000.
Our research team discovered that the leak could potentially have occurred sometime in August 2019, given that the earliest data found on the server aligns with that date.
Customer Impact
The likely impact on customers could be severe if in the wrong hands, given the type of information that was leaked.
A combination of full name, address, marital status are sufficient for nefarious users to conduct identity theft and fraud. Furthermore, personal user details could be used to conduct fraud across other platforms without the victim becoming aware that such activity is occurring.
Therefore, Marriage Tax Refund’s leak could potentially be used to deploy deeper and more damaging scams by sending customized information directly to their target’s addresses, possibly disguised as communication from Marriage Tax Refund, or, disguised as HMRC but referencing the customer’s business with Marriage Tax Refund and thereby gaining the intended target’s trust.
On the flip side, the impact on Marriage Tax Refund is also worth considering. Given the fact that the company allowed its clients and their data to be compromised, this could potentially mean it violated the EU’s General Data Protection Regulation (GDPR) privacy and security laws. The legislation applies to any business that processes personal data from EU citizens or residents, or if it offers goods or services to people living in the EU. Fines for violating GDPR legislation can be as high as €20 million or 4% of total revenue with victims of data breaches being granted the right to seek compensation for damages.
Importantly, the UK is scheduled to leave the EU on 1 January 2021, thereby impacting how GDPR laws apply to UK residents.
The clear and present danger for individuals is that becoming the victim of identity theft is extremely damaging, both financially and reputationally. Moreover, victims of identity fraud experience negative repercussions for a considerable time after their experience because credit history remediation is time-consuming, while financial intermediaries cannot guarantee the full restoration of lost funds.
Furthermore, Marriage Tax Refund took up an intermediary role between its customers and the UK tax authorities, via a “nominated agent” agreement. This means that the company was authorized to deal with customers’ tax affairs directly with the HMRC. If nefarious users obtained the company’s PDF files, they could potentially leverage this modus operandi to send mail to the customer posing as the HMRC, referencing their business with Marriage Tax Refund as a ploy to obtain further information or financial details.
Status of the Data Breach
Our team discovered the vulnerability on 13 October 2020 and promptly attempted to disclose all its findings to Marriage Tax Refund on 14 October 2020.
Having failed to receive a reply from the company, our team first contacted the UK’s Computer Emergency Response Team (CERT) and the Information Commissioner’s Office (ICO) on 26 October 2020, to ensure responsible disclosure of the leak.
CERT informed Website Planet that the case was a “personal breach” which makes it the jurisdiction of the ICO. The ICO responded to Website Planet’s concerns on 30 October 2020 to acknowledge our findings and then again on 3 November 2020 that the case was logged and was presumably being resolved.
Further monitoring showed that Marriage Tax Refund secured its server vulnerability on 6 November 2020.
Protecting Your Data
In this particular case, there was very little customers could have done to safeguard their personal information. Marriage Tax Refund customers became potential victims of identity fraud because the company did not have adequate protection for its data server, or suitable encryption for files that contained multiple pieces of highly sensitive information.
From a customer’s perspective, it is essential to quality check companies that ask for personal information of any kind — especially companies that take on power of attorney and deal on their customer’s behalf with government agencies. It is therefore critical to conduct extensive due diligence on companies including checks on their history, current owners and existing management figures.
In this case, Marriage Tax Refund is registered to a PO Box address with Companies House (UK’s government-run official company list) and neither its owners or management figures can be easily contacted or located.
How and Why We Report on Data Breaches
Website Planet is an entity that seeks to help its readers stay safe when using any website or online service. However, given that most data breaches are never discovered or reported by the affected companies, conveying current risk information can be problematic. As a result, we seek to identify existing online vulnerabilities that are putting people at risk, to better prepare them for the risks they face online.
As an organization, we follow the principles of ethical hacking and we always work within the remit of the law. We only investigate unsecured and unprotected databases that were discovered at random. We never target specific companies and we always report all our findings to the appropriate authorities, including the affected companies themselves.
By reporting these leaks, we help to make the internet safer for everyone.
What is Website Planet?
Website Planet stands as the premier resource for web designers, digital marketers, developers, and businesses operating online. We offer a wide array of helpful tools and resources catering to individuals at all skill levels, from beginners to experts. Furthermore, we provide updates on the most recent advancements in cybersecurity. At the core of our values lie honesty and transparency, which we uphold as our foremost commitments.
We have an experienced team of ethical security research experts who uncover and disclose serious data leaks as part of a free service for the online community. This has included a vulnerability in a Hotel reservation platform and in Donald Trump’s 2020 campaign app.
Read about how we tested five popular web hosts to see how easily hackable they are, here.