Originally published on November 6th, 2020
Company: Prestige Software, based in Spain.
Severity: High
Size: 24.4 GB, totaling 10,000,000+ exposed files
Data Storage Format: Misconfigured AWS S3 bucket
Countries Affected: Worldwide
Courtesy of our security team at Website Planet, we can reveal that a hotel reservation platform has been exposing highly sensitive data from millions of hotel guests worldwide, dating as far back as 2013 and including credit card details for 100,000s of people.
Based in Madrid and Barcelona, Prestige Software sells a channel management platform called Cloud Hospitality to hotels that automates their availability on online booking websites like Expedia and Booking.com.
The company was storing years of credit card data from hotel guests and travel agents without any protection in place, putting millions of people at risk of fraud and online attacks.
Customer Data Exposed
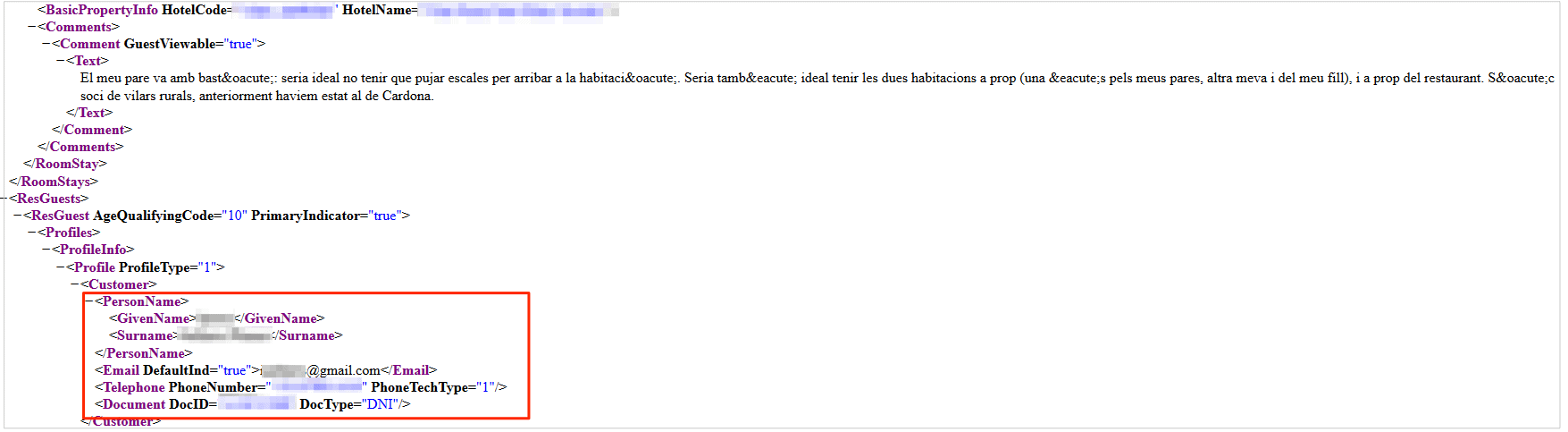
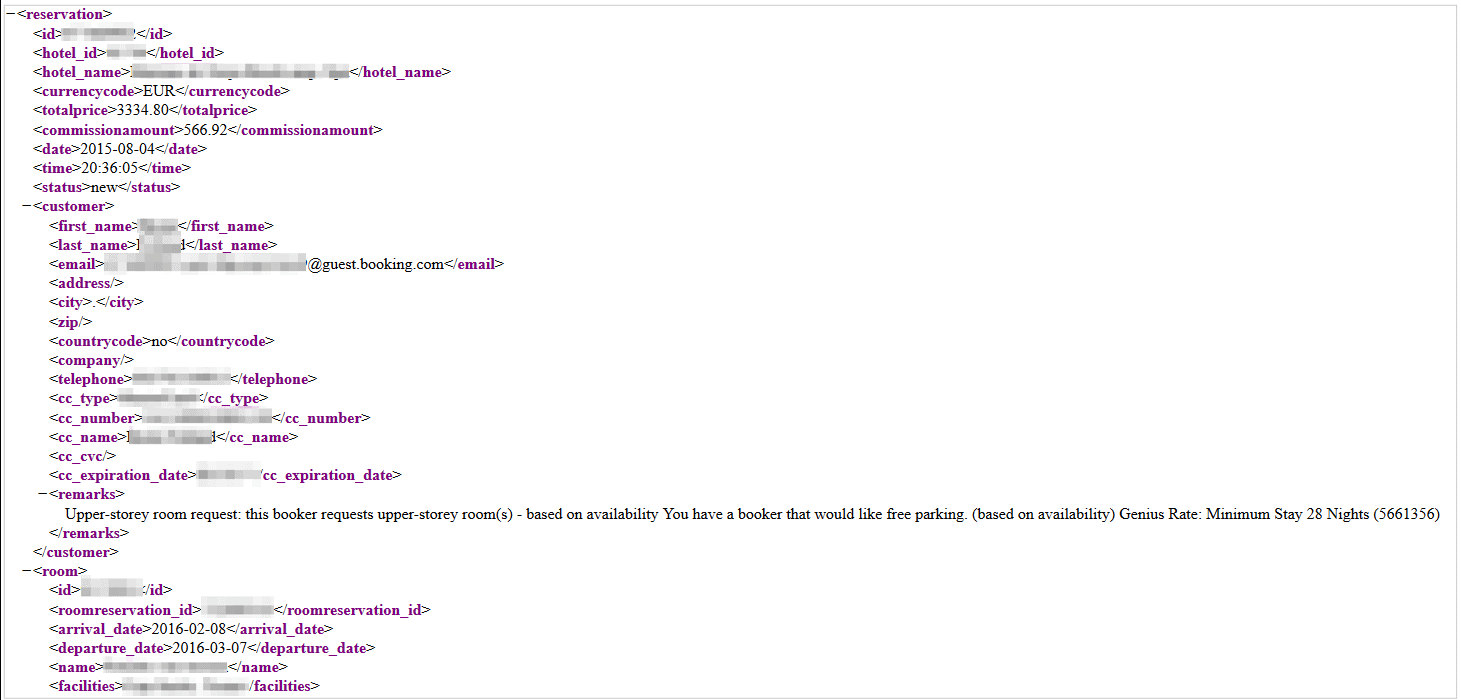
- PII data: Full names, email addresses, national ID numbers, and phone numbers of hotel guests
- Credit card details: card number, cardholder’s name, CVV, and expiration date
- Payment details: total cost of hotel reservations
- Reservation details: Reservation number, dates of a stay, the price paid per night, any additional requests made by guests, number of people, guest names, and much more.
Prestige Software was storing Cloud Hospitality data on a misconfigured Amazon Web Services (AWS) S3 bucket, a popular form of cloud-based data storage.
As a result, a massive amount of data was exposed: over 10 million individual log files in total, dating back to 2013. The S3 bucket was still live and in use, with new records being uploaded within a few hours of our investigation.
The S3 bucket contained over 180,000 records from August 2020 alone. Many of them related to hotel reservations being made on numerous websites, despite global hotel bookings being at an all-time low for this period.
Each of these records exposed sensitive and valuable Personally Identifiable Information (PII) data belonging to the individuals making the reservations.
However, it’s difficult to say how many people were affected, due to the amount of data exposed. Furthermore, many of the data logs contained PII data for numerous people on one reservation (families, for example). Finally, some of the data logs included amendments and cancellations.
For these reasons, the actual number of people exposed could be much higher than the number of reservations logged.
The screenshots below were taken within the S3 bucket and show how sensitive PII and credit card data were exposed through reservations being recorded by the channel manager.
Based on the detailed credit card data exposed in this breach, Prestige Software has breached the Payment Card Industry Data Security Standard, known as PCI DSS.
The PCI DSS is an information security standard set by the major credit card companies to reduce fraud against their customers by setting protocols for how companies store, transmit, and handle all credit card data.
Non-compliance to the PCI DSS or a breach of its protocols by a company or online vendor can result in having the ability to accept and process credit card payments stripped.
Websites Affected
Based on the volume of data stored in the database, Prestige Software’s channel manager, Cloud Hospitality, is a popular solution. Not only has it remained in active use during the Coronavirus crisis, but it’s also connected to many of the biggest hotel booking websites in the world.
Prestige Software doesn’t list its clients on its website. However, the S3 bucket contained data that appeared to originate from many well-known sources listed as Cloud Hospitality’s customers, including, but not limited to:
- Agoda
- Amadeus
- Booking.com
- Expedia
- Hotels.com
- Hotelbeds
- Omnibees
- Sabre
- and many others
*Note: we didn’t review all the files exposed in the S3 bucket, so this isn’t a complete list. Every website and booking platform connected to Cloud Hospitality was probably affected. These websites are not responsible for any data exposed as a result.
Who Was Leaking the Data?
Prestige Software’s main product, Cloud Hospitality, is a channel manager.
A channel manager is used to connect online reservations websites like Booking.com and Expedia with the software used by a hotel to manage its availability and vacancies. The channel manager ensures that the availability of a hotel’s rooms is updated and distributed across every relevant website (sometimes 100s of websites).
For example, when you book a room at a hotel on Agoda, that room will no longer be available for someone else to reserve on Expedia.
Cloud Hospitality is used by hotels listing accommodation on many of the biggest hotel booking websites and Online Travel Agents (OTAs) in the world, alongside traditional travel agents reserving rooms for their clients.
Impact on Hotel Guests
Millions of people were potentially exposed in the data breach, from all over the world.
We can’t guarantee that somebody hasn’t already accessed the S3 bucket and stolen the data before we found it.
So far, there is no evidence of this happening. However, if it did, there would be enormous implications for the privacy, security, and financial wellbeing of those exposed.
Credit Card Fraud Identity Theft
Cybercriminals could use the exposed PII data and credit card information to commit credit card fraud and steal from people compromised in the breach.
Furthermore, the same data could be used in other forms of financial fraud or identity theft.
Scams, Phishing and Malware
Cybercriminals could use contact information exposed in the breach to target hotel guests with scams, phishing campaigns, and malware attacks.
With the PII data from the leak, it would be easy to establish trust and encourage people to click on links embedded with malware or provide valuable private data.
Cybercriminals could use details of hotel stays to create convincing scams and target wealthy individuals who have stayed at expensive hotels for maximum reward on their schemes.
Finally, if any hotel stays revealed embarrassing or compromising info about a person’s life, used to blackmail and extort them.
Reservation Takeover
With detailed information about a person’s hotel reservation, a hacker with access to the exposed files could take these details, contact the hotel, and change the dates and names on the reservation.
They could then take over someone’s holiday without paying, or pose as a travel agent and sell the reservations to unsuspecting customers. They could, of course, do this more than once.
Impact on Prestige Software
GDPR and Data Privacy Violations
Prestige Software is based in Spain, an EU country, and it has been processing the data for many people across the EU.
This puts it squarely within the jurisdiction of the trade bloc’s GDPR data regulations. As a result, the company must follow strict rules for reporting the breach and ensuring there are no more vulnerabilities in its systems.
If it fails to do so, it may face legal actions and huge fines from the EU.
Loss of Business
Prestige Software faces losing huge amounts of business due to this data breach. If hotels and OTAs don’t trust the company to protect their customers’ data, or feel they will be liable for any damage caused by this one, they may switch to an alternative solution.
The market for channel managers is saturated and highly competitive. Any business that wants to change providers will have plenty of options.
Furthermore, by breaching the PCI Standard, Prestige Software may lose the ability to handle credit card information in the future. If so, it would be unable to accept credit card payments, making it almost impossible for the company to operate.
Negative Press Coverage
Prestige Software exposed the private data and credit card details of millions of people worldwide, spanning almost a decade.
The international travel and hospitality industries have been devastated by the Coronavirus crisis, with many companies struggling to survive, and millions of people out of work.
By exposing so much data and putting so many people at risk in such a delicate time, Prestige Software could face a PR disaster due to this breach.
Once again, given the abundance of options in the channel management industry, clients and partners may decide to publicly distance themselves from the company as a result.
Meanwhile, competitors could exploit the story’s coverage to convert clients over to rival platforms, taking huge chunks of revenue with them.
Status of the Data Breach
We investigated several companies potentially responsible for the data breach. However, considering the size of the data exposed and its sensitivity, we decided to contact AWS directly so it could resolve the issue quickly and ensure the breach was closed.
The S3 bucket was secured the following day.
In the meantime, we continued our investigation. We also confirmed that the data was real by taking a sample of email addresses exposed in the leak and verifying they belonged to real people.
Eventually, we confirmed Prestige Software as the owner of the data, and the party responsible for the leak, and reached out to the company.
The company confirmed it owned the data shortly after.
Unfortunately, given the number of hotel and travel websites affected in this breach, it’s impossible to help anyone already exposed if somebody found the data before us.
Protecting Your Data
If you’re a customer of any of the websites listed in this report and are concerned about how this leak might impact you, contact the company directly to determine what steps it’s taking to protect your data.
For OTAs and Travel Companies
Thoroughly vet all 3rd party software providers and solutions. Ask for proof of auditing and regular security monitoring.
If Prestige Software exposed your customers’ data, you need to inform the customers they may need to cancel their cards and take the appropriate steps to protect their identity.
How and Why We Report on Data Breaches
We want to help our readers stay safe when using any website or online product.
Unfortunately, most data breaches are never discovered or reported by the companies responsible. So, we decided to do the work and find the vulnerabilities putting people at risk.
We follow the principles of ethical hacking and stay within the law. We only investigate open, unprotected databases that we find randomly, and we never target specific companies.
By reporting these leaks, make the internet safer for everyone.
What is Website Planet?
Website Planet stands as the top resource for web designers, digital marketers, developers, and businesses with an online presence. We offer tools and resources catering to all levels, from beginners to experts — and we prioritize honesty above all else.
We have an experienced team of ethical security research experts who uncover and disclose serious data leaks as part of a free service for the online community at large. This has included a vulnerability in Donald Trump’s 2020 campaign app and a website builder for churches around the world leaking private data.
You can read about how we tested five popular web hosts to see how easily hackable they are here.