Global Online Retailer Leaked 1.1 Billion Records Online Including Customer Data
Security researcher Jeremiah Fowler together with the Website Planet research team discovered a non-password protected database that contained a massive amount of records. The total size of the dataset was 601.84 GB and the total number of documents were over 1,16B. Upon further research there were multiple references throughout the database indicating that the data belonged to the California-based online retailer, Vevor. According to Crunchbase they are registered in the US, but based on publicly available details on their website (for e.g. privacy policy), it appears to be a China-based company.
According to their website: “VEVOR is a leading brand that specializes in equipment and tools. Along with thousands of motivated employees, VEVOR is dedicated to providing DIYers and professionals with tough equipment & tools at the lowest prices. Today, VEVOR has satisfied over 10 million customers in more than 200 countries and regions.”
Two separate data exposures:
The first database was initially discovered back in early April 2022 and despite multiple responsible disclosure notices we never received a reply and the database was restricted from public access several days later. Then, on a separate IP address, the unsecured AWS server appeared again in early July 2022, when we again tried to reach out to the owner, yet again, we didn’t receive a reply, luckily the server was shortly secured. The misconfiguration was caused by the server’s owner (VEVOR or their infrastructure vendor) and not Amazon Web Services.
The data was marked as “production” and contained what appears to be various types of PII and sensitive data relating to their online operations including customer information such as first and last name, partial credit card numbers, transaction IDs, order and refund information, and much more. The payment and checkout records including names, emails, home addresses, currency, and more were exposed in both plain text and hashed.
Since July, we haven’t seen the dataset exposed again. To make sure it wouldn’t appear again online and ill-intentioned hackers would find it, we waited a few months before publishing our findings.
What the database contained:
1st Exposure in April 2022: Total Size: 406.79 GB / Total Documents: 706,206,770
2nd Exposure in July 2022: Total Size: 601.84 GB / Total Documents: 1,166,293,742
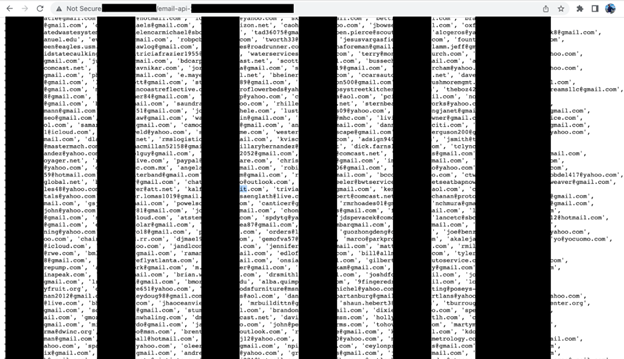
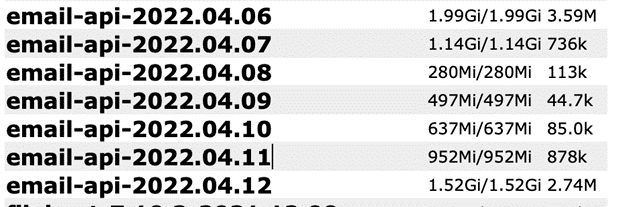
- A very large number of email addresses: There were 7 folders named “email-API” with 8.1 million records, which comes up to about 31.64GB in total. Based on a limited sampling of 10,000 records, were found 2,559 email addresses that appeared to be unique.
- 12.9 Million records in folders named “Members” (some of which we were unable to categorize). However, it appears that not all of these records contained customer names in plain text. Based on tests conducted with limited sample size, we were able to match unique user ID numbers available and match it to other areas of the database.
- Records with multiple Localized Domains: .COM, .DE, .CO.UK, .CA, .IT, .ES, .FR, .AU. According to their about us page, VEVOR claims a global presence, with warehouse operations and offices located in multiple countries.
- Error messages that were written in Chinese as well as internal images and other files that were hosted on amazonaws.com.cn.
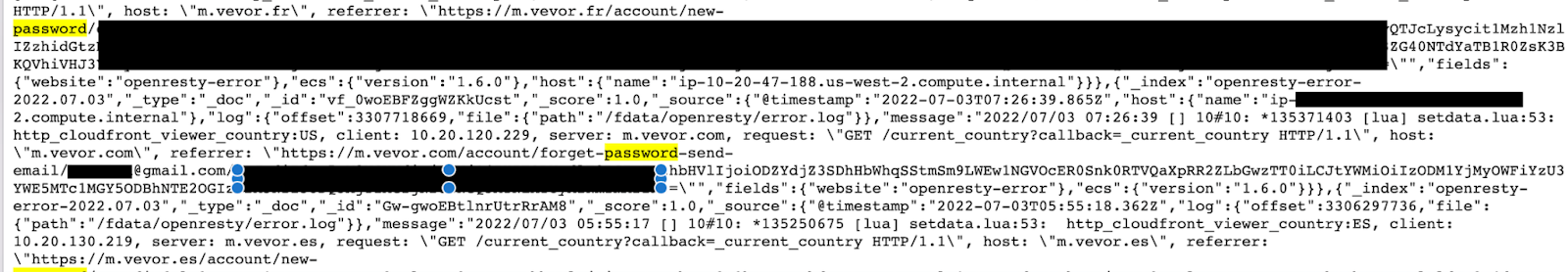
- Internal Vevor account admin names and what appeared to be plaintext passwords.
- Active Password Reset Links.
- Partial credit card numbers, references to passports and tax numbers.
- IP addresses, Ports, Pathways, middleware, and storage info that cybercriminals could exploit to access systems or services. Overall, the exposure provided a complete look at Vevor’s operating structure, logging, monitoring and error records, and more.
- Configuration information that could be used to penetrate deeper in the network.
- The database was misconfigured and left open and publicly accessible in any browserand anyone could edit, download, or even delete data without administrative credentials. As legitimate security researchers we never edit, delete, or modify data that we discover and only take a limited number of samples for research purposes.



Massive Amount of Records
For ethical reasons we do not download the data and only sample a limited number of records to validate our findings and get an estimate of the size or scale of the data. With over a billion records and a limited amount of time to review this massive dataset, it is hard to assess exactly how many individuals may have been affected or the total number of emails the database contained. It is also unclear how long the first instance was exposed or who else may have had access to the treasure trove of data that was exposed to anyone with an internet connection.
Data Exposure Impact:
We cannot determine whether malicious actors have gained access to the database. Nevertheless, if such individuals have indeed breached the database, they might utilize its data for the purpose of engaging in criminal activities targeted towards users.
- Phishing. Criminals can conduct targeted phishing campaigns against victims when they know private or internal information about the target. Hypothetically a cybercriminal could send emails that reference their recent purchase from Vevor and ask the customer to update their payment information on a cloned website or even via email. They could also send an email asking the target to unsubscribe from marketing emails, validate or change their account password, and a wide range of other creative fraudulent activities. The victim would have no reason to not trust the communications using inside information that only the seller and the customer would know.
- Potential financial fraud: By combining the PII exposed by Vevor with any additional information extracted through successful phishing campaigns, cybercriminals could pursue countless forms of fraud and cyber theft. Exposed payment information of any kind is a massive risk for any organization. Financial gain is the primary goal of nearly 90% of cybercrimes. We saw multiple references to payments such as PayPal*, credit cards and a service called Klarna* (a Swedish fintech company that provides online financial services such as payments for online storefronts and offers “buy now pay later” payments). Klarna can be used on purchases made on Vevor for orders between $35 and $1000. One potential risk of exposing payment records is seeing what customers use as payment methods. These customers can then be divided for example into those who pay with PayPal*, those who use Klarna*, etc. Cybercriminals could then try to hack their accounts using the known email associated with the payment service. They can also socially engineer the customer to gain access to their email account and unlawfully make purchases to a new address using the victim’s financing account.
(*: note neither PayPal nor Klarna have been exposed in this breach, and aren’t responsible of the exposure of their customers)
- Unauthorized access: The unencrypted admin usernames and passwords exposed in this breach may allow malicious parties to access Vevor’s backend files and customer user accounts. We didn’t log into any user accounts for ethical reasons, but this was easily accessible. Spam: Email spam can be dangerous and the reason criminals still use this old method is because it works. Spam can include malicious links, attachments, or images that can infect your device with malware.
Possible risk of password reset poisoning
This database was publicly accessible and it was possible for malicious actors to delete, alter, or edit the records including inserting malicious code. As ethical researchers we do not alter the data we see. Password reset poisoning is an older attack method that does not get much attention these days, but is still hypothetically possible. In this context, password reset poisoning may occur when malicious actors manipulate the vulnerable website into generating a password reset link, redirecting the link to a fraudulent domain under their control. This domain is then leveraged to steal the secret tokens required to reset users’ passwords and, ultimately, compromise their accounts.
Past Legal Issues
For completeness, public web searches have led us to understand that VEVOR is party to several intellectual property infringement lawsuits (settled and ongoing).
VEVOR has faced a series of lawsuits for copyright infringement and copying well-known products dating all the way back to 2016.
- In March 2016, VEVOR settled a federal lawsuit for selling cloned copies of press manufacturer Stahls’ products and Hotronix Fusion’s patented technology, trademarks and copyrighted content.
- In January 2020, General Wire Spring Company filed an intellectual property and trademark lawsuit against VEVOR Corporation.
- Smoky Lake Maple Products posted on their website in February 2020 that VEVOR claimed to sell Badgerland brand pans for making syrup and had stolen their photographs and texts.
- In December 2021, Motion Pro filed a patent lawsuit against VEVOR for copying and selling Motion Pro’s BeadPro, which was marketed as the Motorcycle Tire Iron calling it the Vevor “tire tool”.
- In March 2022, Summit Tool Company doing business as Ken-Tool filed a lawsuit against VEVOR Corporation.
In June 2022, Nautilus Inc. filed a lawsuit alleging that VEVOR Corporation sells adjustable dumbbells that were developed by copying its patented technology.Also in June, 2022 the UK government rejected the import of multiple VEVOR tools and welders. According to the UK Office for Product Safety and Standards the VEVOR products were destroyed at the border because they were unsafe and the risks of electric shock and burns to consumers.
Upon making any discovery, our key prerogative is to highlight security vulnerabilities surrounding our discovery. Our usual process would be to provide a brief overview on potential data owners, what was in the records, and provide a narrative on how information revealed may pose potential privacy and / or cybersecurity risks. It must be emphasized that we do not point fingers, and are not implying any wrongdoing by Vevor or their partners. Our findings are published solely for educational purposes of cyber security best practices.