Please describe the background behind VMWare and Carbon Black, who they are, and why they joined forces
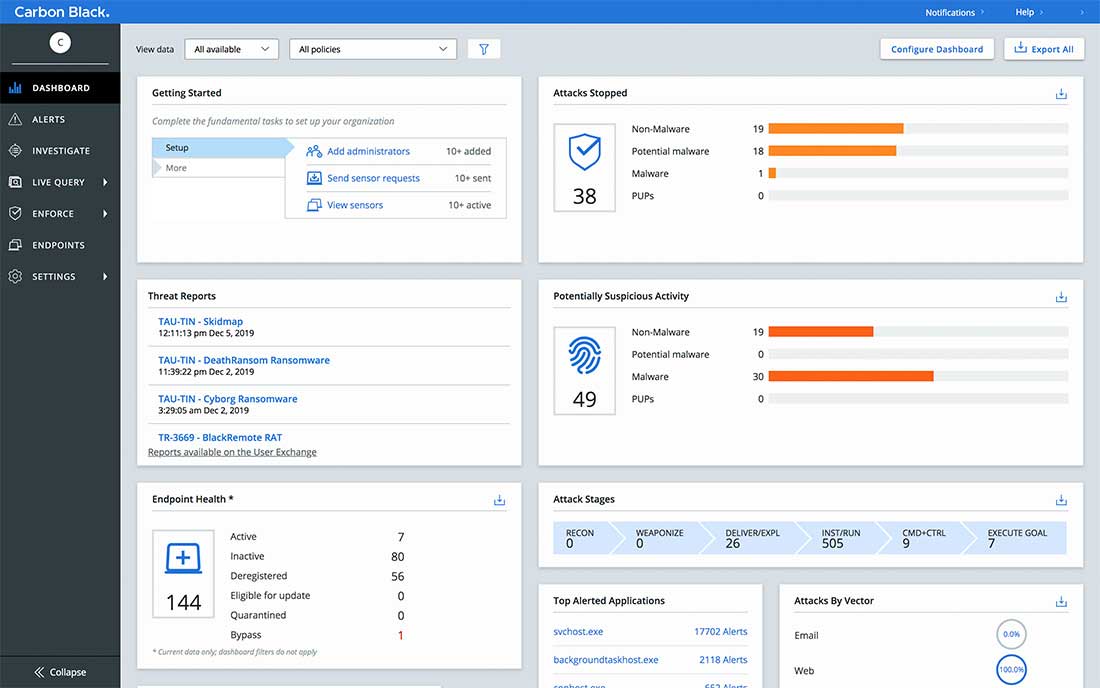
I’ll take you through this journey from my own perspective, the Carbon Black perspective. Carbon Black as an entity has been around for 17 years, so it’s a fairly long-standing cybersecurity company. It started by creating a market space and technology which was referred to as application control. As a product, Carbon Black is largely deployed in very secure areas, where organizations only allow good known executables to run and ban everything else. Subsequent and a few years later, 5-6 people were working in a garage on an issue that crossed boundaries, from government entities to commercial enterprises. That was called Operation Aurora. It was a nation-state that started targeting commercial cloud providers, departments of defense, and government entities. The technology to record activities on an endpoint didn’t exist, and there was no data to figure that out with. So that team created it, which led to the formation of a brand new market called Endpoint Detection and Response (EDR). Subsequent to starting EDR an acquisition of another organization was made to provide next-gen antivirus and a cloud platform, and bring those two solutions together. After we launched our cloud technology, bringing on-prem solutions into the cloud, we went public in 2018 and then were acquired by VMware in late 2019. So now we’re actually serving as part of the security business unit for VMWare. VMware has an awesome history. It started off in the late 90s, essentially creating virtualization technology that 80% of all providers use. If you’re running a data center, there’s a good chance you’re a VMware customer. So for us, it represents the opportunity to not only build security for 80% of that market space, but also to provide intrinsic solutions – security that’s baked into the fabric of existing technology. Too many people simply bolt security on. VMware’s intrinsic security strategy means customers can simplify and strengthen security. Essentially, anytime you deploy a virtual machine server, our technology will be there, automatically deployed as part of the toolset, and transparent to all users. What we’re trying to do is simplify and reduce the number of controls teams need, and allow them to focus on the important stuff. That’s the journey we’re on in 2020. Here’s a quick preview of what the VMware Carbon Black dashboard looks like: