ImmuniWeb provides AI-enabled Application Security Testing, Attack Surface Management solutions, and Dark Web monitoring tailored to reduce complexity and operational costs. In this eye-opening interview, ImmuniWeb founder and CEO Ilia Kolochenko discusses the threats, challenges, opportunities, and regulations that make up the cybersecurity landscape today.
Please describe your background and the story behind the company: What sparked the idea, and how has it evolved so far?
I started my very first job in cybersecurity when I was about 17 years old. At the time, it was labeled “ethical hacking”, but the essence was fairly the same. I’ve been doing penetration testing and security auditing for almost 15 years.
In 2016 I decided to augment my technical skills with some humanitarian studies, so I started a master’s degree in legal studies at Washington University in St. Louis and I successfully graduated in 2018. This year I will be finishing my second master’s degree in criminal justice and cybercrime investigation at Boston University.
I’m putting everything that I’ve learned into practice so not only can I explain, elaborate, and disassemble the technical elements, I can also explain the business and legal consequences.
ImmuniWeb is a company fully dedicated to application security. We offer a full spectrum of services related to application security testing and protection, attack surface management, and dark web monitoring that enable our clients to make risk-based, threat-aware, and well-informed decisions.
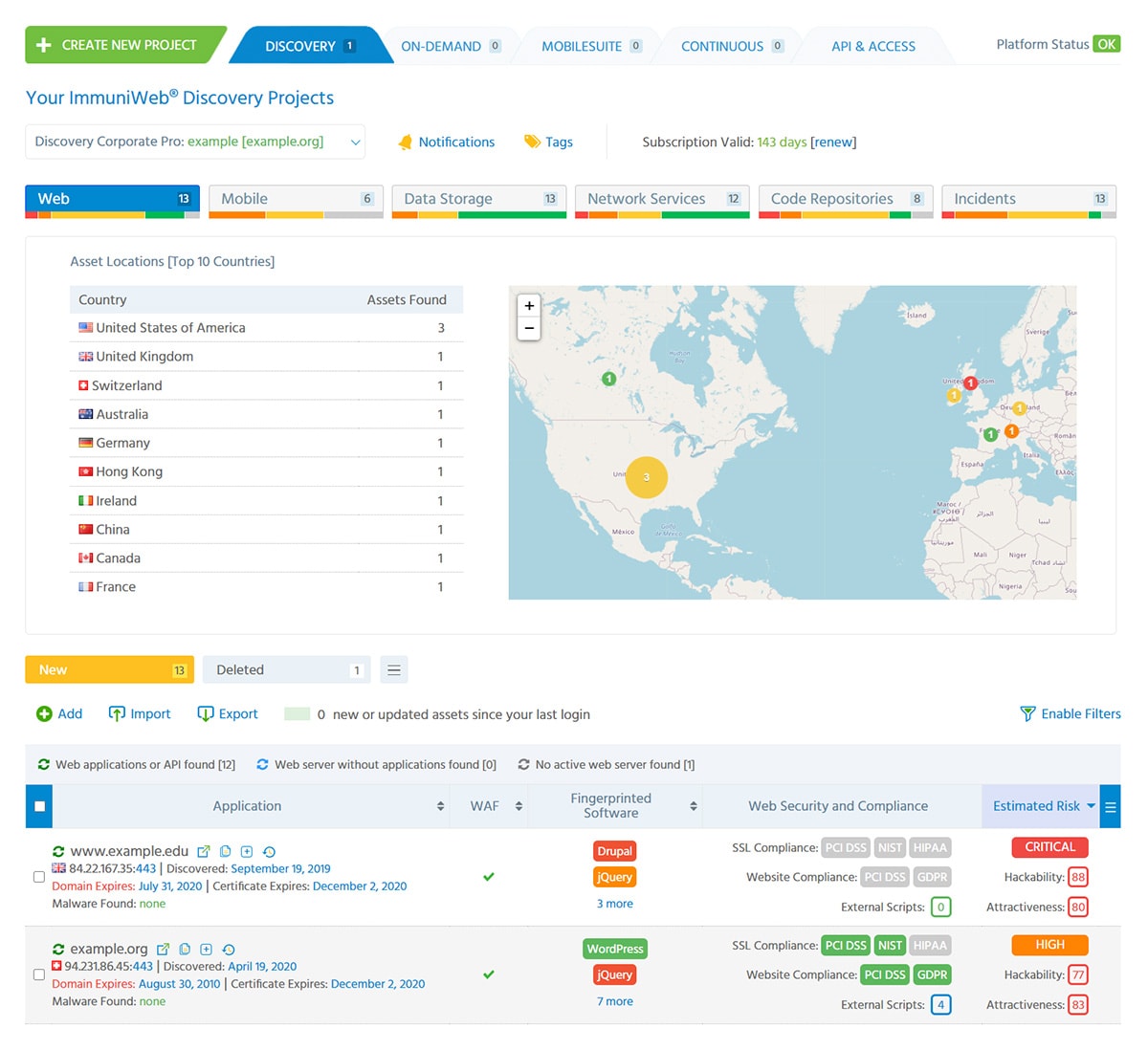
Here’s a sneak peak into ImmuniWeb’s AI Security Platform.
One of the biggest dangers on the market today is that many organizations do not have a comprehensive inventory of their applications, databases, APIs, and all the different systems and IT assets they have in place. They cannot protect what they can’t see. So at the end of the day, all of their efforts and investments in application security can be at risk just because of one forgotten application, server or database, abandoned in the wild.
ImmuniWeb provides true visibility of your assets, risks and threats, including in-depth visibility of your deep and dark web exposure. Being able to see your own assets is essential, but on the dark web, you can get a lot of insights not just about your organization, but about data, accounts, or passwords that have been stolen from your trusted third-parties.
The majority of critical and sensitive information that we detect for our clients on the dark web belonged to their suppliers, IT and cybersecurity vendors included. It’s a huge and rapidly growing problem because organizations have to outsource and delegate tasks and processes to presumably trusted third parties who are competing with each other. In light of COVID-19, many of them have had to cut their cybersecurity and data protection costs, eventually exposing their clients and customers to a wide spectrum of digital risks and threats. We bring them full visibility and enable comprehensive, inclusive application security testing and defense.
ImmuniWeb is one of the most inclusive platforms out there; not only does it provide you with testing and protection, but it also gives you the ability to apportion the resources and time you have in a well-thought, holistic and data-driven manner.
You mentioned compliance with privacy regulations which is something that a lot of businesses are struggling with. If you were a policymaker, how would you change those policies to make compliance easier?
To answer your question, I’ll start with some thoughts about GDPR. What we see now is a growing amount of fraud that is fostered by GDPR. For example, we have reports and researches about cybercriminals usurping the identity of real customers and sending legal threats to different organizations saying “you unlawfully collected my personal data, please send me everything you have on me as required by the GDPR”.
Many organizations still do not have clear legal guidelines as to how to handle such inquiries and verifying identity. Most of them don’t have an in-house legal counselor who can provide competent legal advice. By acting in good faith, these organizations may unwittingly share all your data, including payment information and account records, with third parties, who will, in turn, usurp your identity. All this is actually enabled by GDPR, and its harsh penalties, advertised by some security vendors and media, are abstracted from the context. Obviously, I’m not saying that GDPR is bad per se, but as a collateral effect, it facilitates new vectors of phishing, social engineering, and fraud.
Secondly, we’re starting to see companies that prefer to dedicate more resources to paper-based compliance, rather than practical cybersecurity. They don’t really care if they’re silently being hacked because everyone gets hacked. They focus their efforts on getting compliance on paper so that even if they’re hacked, they will be able to prove that they’ve made reasonable efforts to prevent it. Thinking that will lower the damage made for the business is a big mistake.
I’ll also say that enforcement of GDPR is becoming very peculiar these days. According to the most recent report by the European Commission, most of the fines are being imposed upon large organizations like BA in the UK.
Some legal scholars say that GDPR may be a lawful means to extort too-big-to-fail organizations by saying, “you are big, you have money, so you’ll pay us.” Some states are visibly trying to leverage GDPR as a new means to collect additional “taxes”.
At the same time, when we’re dealing with small organizations, there are practically no security policies whatsoever, outrageously exposing commercialized personal data without consent. They usually have a fairly nominal fine of 1000 Euros or so, despite the fact that their profits from these unlawful activities are probably 10 times higher. I don’t think this growing imbalance and disproportional enforcement were the initial purposes of GDPR.
Even though GDPR is presumed to be enforced globally, many companies around the world choose to ignore it. For example, if you have a company located in China that mishandles the PII of European citizens, you can’t do anything unless that company has a subsidiary or some kind of legal foothold in the European Union, such as owning a property. This created a growing problem of “judgment-proof” companies.
Most of the compliance strategies are becoming extremely complex because of the increase in new regulations, like the new California Consumer Privacy Act (CCPA).
Today, the European Union and the United States openly disagree about data protection. I think European companies may start ignoring applicable laws from the United States, and vice versa, leading to growing instability and uncertainty.
I think other US states will try to bring their own GDPR-like privacy laws, potentially resulting in conflict. What we really need is unified legislation, protection, and enforcement, otherwise, it will be unfeasible to comply with all applicable laws.
If the situation continues, enterprises will start ignoring global regulatory requirements, focusing only their local ones. If they have 100 overlapping and contradicting compliance requirements to adhere to, they would prefer to pay a fine or even cease from doing business at a specific state or country because economically, it’s impractical. I think we’re arriving at the point where too much regulation would start damaging international business, and kill all those good things that data protection policies can eventually bring to our society.
Enforcement seems to be mainly focused on compliance by companies, but we don’t see much effort invested in catching cybercriminals. What are your thoughts about that?
I agree. When we’re talking about cybercriminals and not just careless, negligent organizations, many of the sophisticated gangs are enjoying impunity. They have cryptocurrencies, and not necessarily Bitcoin which, under a narrow set of circumstances, can be traceable. We’re talking about specific cryptocurrencies that ensure 99.99% anonymity, so they are technically impossible to trace and to and investigate them.
10 years ago, cyber gangs had to find a reliable partner to launder their money, either through PayPal accounts or banks where they could collect their gains and then obtain it as cash. Today, practically speaking, if the cyber gang is organizing their raids in a well-thought manner, it’s technically impossible to find them. Obviously, law enforcement agencies may try to infer who may have benefited from a specific attack, or get a hint from ex-criminals or accomplices, but if you don’t have such insider information or any other hints, most of the sophisticated nation-state and APT attacks are untraceable.
How would you say COVID-19 affected your business particularly and the industry as a whole?
I think that COVID-19 has brought a lot of changes by exacerbating the problems we already had. Thus, from a practical standpoint, there is really nothing new. COVID has only vulgarized and emphasized the problems that we had for many years.
For example, organizations are now urgently creating work from home infrastructure, exposing their VPNs, databases, and internal CRMs to the internet. Previously, we had many organizations that had databases exposed for years and they didn’t care. Nowadays, the number of exposed systems that are not supposed to be accessed from the outside is skyrocketing.
We also have a growing challenge of Phishing and social engineering attacks. Again, unfortunately, it’s nothing new, but new vectors are now being utilized to steal credentials and personal data for efficient social engineering. Given that employees have privileges and sometimes uncontrolled access to the Crown Jewels, many spear-phishing campaigns become unprecedentedly successful and fruitful. Hence, I think the number of phishing attacks will continue to grow.
Another challenge we see is that cybersecurity budgets are being reduced amidst the pandemic. Common sense suggests that they should be increased, but given that many companies have suffered severe economic damage, they have to cut their spending everywhere, including cybersecurity. I don’t think that it’s a wise move, but some organizations are obliged to do so in order to survive. Given this situation, we can expect major challenges to all the organizations that are now operating with smaller teams, smaller budgets, and a growing number of threats and intrusion attempts.
How do you envision the future of your industry?
I think it will largely depend on the economy. So far cybersecurity is steadily growing, but we see that contrasted to cybercrime, cybersecurity startups are fairly far from being efficient and effective. We have many examples where startups say, ok, we failed to deliver our promises but we’ll ask our investors for more money and then we’ll try again.
In any case, sooner or later we’ll see a consolidation of the market. We have thousands of smaller players, offering overlapping or even identical solutions without any substantial difference between them. They are mostly competing by pricing, packages, or by aggressive marketing campaigns. That’s not bad per se, but this imbalance is a challenge we need to address.
In a few years, startups that do not have highly competitive and innovative technologies, but instead rely merely on VC funding to grow, may disappear from the market landscape.
However, startups that do have genuine innovation that can bring value and excellence to their customers and partners are likely to flourish. They will be highly successful for a long period of time and will manage to overcome the economic crisis even as many organizations cut down their cybersecurity budgets.
I will conclude that Cybersecurity is the place to be, however, unlike 2016 for example, these days competition is comparatively tougher. Companies who wish to survive have to competitively deliver value, excellence, efficiency, and effectiveness. If you’re capable of providing genuine innovation, it’s a great time to be in the Cybersecurity space as the market is still very much in its early days.