Security researcher Jeremiah Fowler together with the Website Planet research team discovered a non-password protected database that contained a total of 170,239 records. The data contained details of medical workers, nurses, and caregivers. These employee profiles exposed names, phone, email, home addresses. The accounts also contained links to images of the employees, and files that indicated credentials, and tax documents (SSN / Social Security Number).
There were multiple references to “UseGale” in the dataset. The files included internal email addresses, usernames, and administrative passwords in plain text. There were records in the folder named “Employees” that contained the @usegale.com domain with indications of “internal corp employee”. This domain is used to promote the mobile application of the healthcare staffing company Gale Healthcare Solutions. We immediately sent a responsible disclosure notice to multiple addresses and public access was closed the same day.
According to their website “The Gale app uses the latest mobile technology to connect healthcare facilities in need of clinical talent with our large network of local available nurses and caregivers. With Gale, facilities can fill open shifts within seconds, easily stay on top of compliance and never worry about short-staffing again”.
What Data Was Exposed:
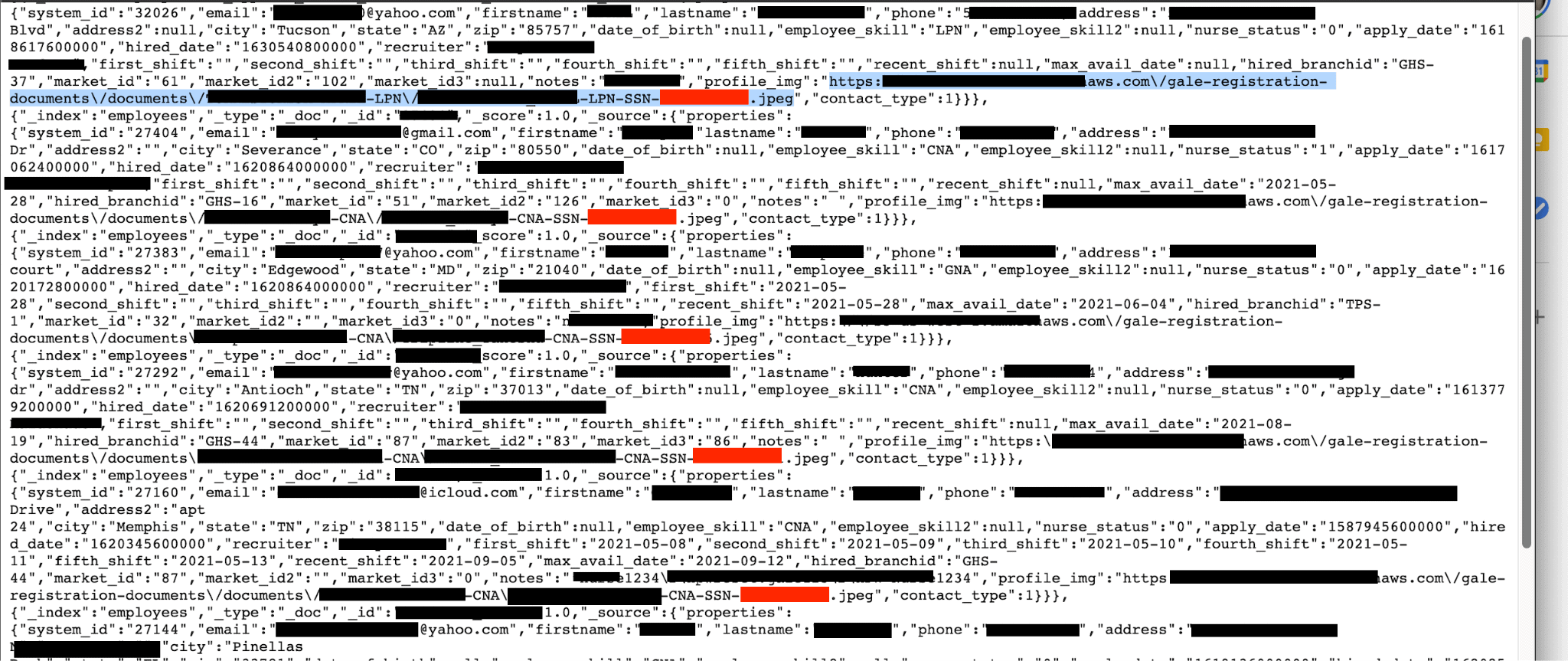
- Total Number of Records: 170,239 in two folders. Contacts 139k and Employees 31.5k. (In a large sampling of records it appears these were unique and without duplicates)
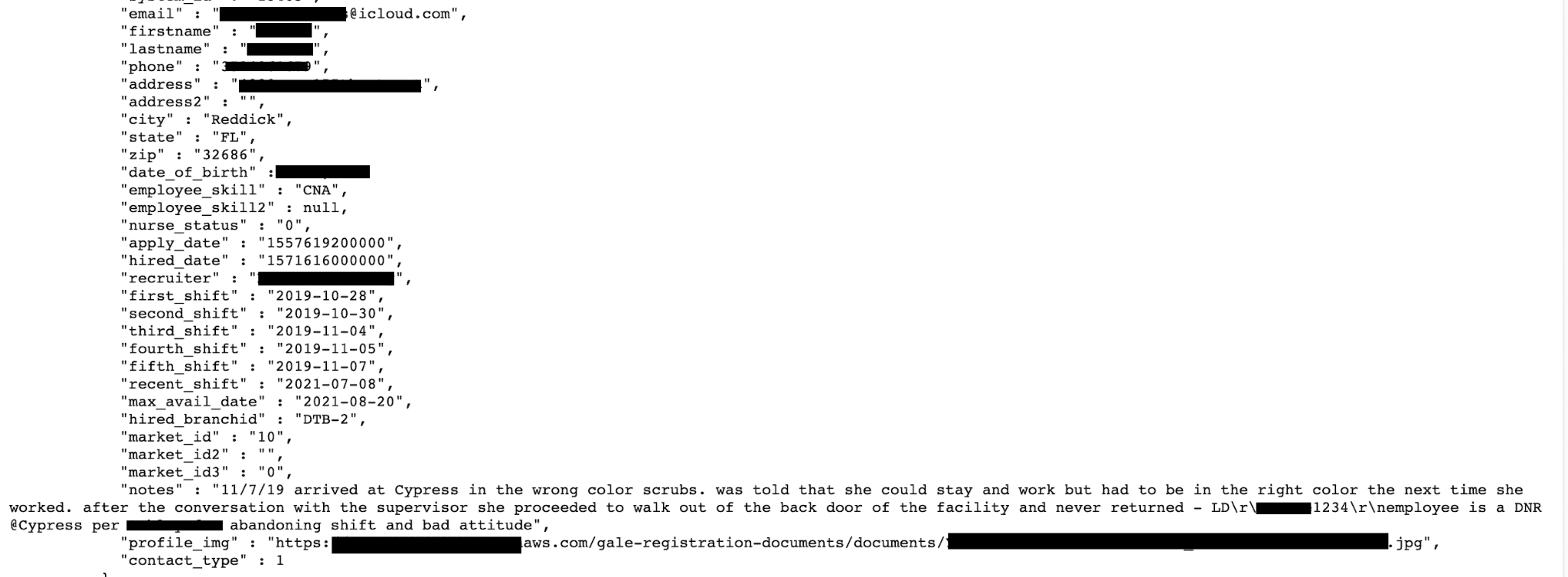
- Internal records that include first and last names, phone, emails, home addresses, hire dates, apply dates, skill level, and some had detailed notes of incidents and terminations.
- Passwords in plain text, usernames appeared to be the user’s name or email address that was also listed in the account. We assume this allowed access into the application or employee portal.
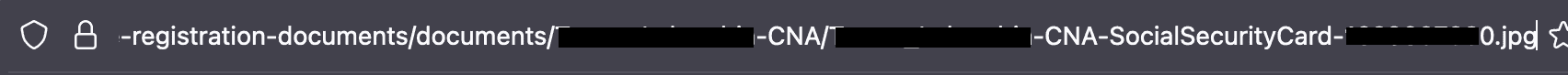
- links to AWS storage accounts that contained photos of the employee and files named “SSN Card” or “credentials”
- Images were in a format that contained the employees’ full name and a number titled “SSN” in the file name. Here is an example of a file name : https://REDACTED.com/gale-registration-documents/documents/Jane-Doe-CNA/Jane_Doe-CNA-SocialSecurityCard-123456789.jpeg
- This exposed data could be used for a range of crimes including identity theft, scams, and extortion. With email addresses cyber criminals could launch a targeted phishing campaign or social engineering attack using insider information to establish trust.
- The storage files also exposed where the data is stored and the sub folders that could have been a secondary target.
- Detailed records of the discipline, firing, and other work related problems that should not be publicly exposed.
The Risk of This Kind of Exposure
Employment records are a treasure trove of information for both employers and cyber criminals. Identity theft is a nightmare that can take years to recover from and cause significant financial harm in the process. Criminals use personally identifiable information such as your name, Social Security Number, and home address for their personal financial gain.
Once a criminal has the necessary data they can apply for credit cards, loans, services, file fraudulent tax returns, and more. This information can be collected and sold to other criminals worldwide via the dark web. Many of these criminals are located in parts of the world where it is almost impossible to bring them to justice for their crimes. The total cost of identity theft in 2020 was a record breaking $56 billion. With so much money to be gained it is clear that identity theft and fraud is not going anywhere anytime soon.
Weak passwords are a very big security threat. Easy passwords and reused passwords can allow unauthorised access to accounts, account takeovers, data theft, and other forms of cyber attacks. In a sampling of 10,000 records, “Password” appeared 2,921 times. We could also see multiple internal Admin accounts that used very similar and easy passwords. We highly recommend that organizations and users alike use complex passwords for any account that contains sensitive user data. The security standard of a strong password should contain a minimum of 12 characters. These should be a combination of uppercase and lowercase letters, numbers, and include any special characters.
File Security and Document Names
Image or file names can also be a data security risk. Organizations who collect and store data usually use internal ID numbers or other methods that conceal or hide any personal data on file names or folder names. This is the first time I have ever seen full names and a number called “SSN” in the actual file name. In theory the file wouldn’t have to be opened to expose sensitive data because the file name alone contained what appeared to be PII (personally identifiable information).
The Covid 19 pandemic has hit healthcare workers hard with long hours and many are physically and emotionally exhausted. Hospitals all over the United States are suffering from a shortage of healthcare workers. Any service that allows hospitals to fill their shifts is extremely important and valuable to sick patients. It is unfortunate that this incident may have exposed the data of frontline workers during an already difficult time. Healthcare workers’ private information publicly available also poses a risk of unwanted harassment, intimidation, or cyber stalking.
We do not know the duration of the database exposure or who else might have accessed the publicly accessible records. Additionally, it remains uncertain whether medical workers or authorities were informed of the potential exposure, as mandated by the Florida Information Protection Act of 2014 (FIPA).
We are not implying any wrongdoing by Gale Healthcare Solutions, their partners, or users and we are highlighting our discovery to raise data protection awareness and promote cybersecurity best practices. Our mission is data protection and securing information that is publicly exposed. Public access was restricted within hours after we sent a responsible disclosure notice to Gale Healthcare Solutions. We have not received any reply from Gale Healthcare Solutions at the time of publication. We do not download or extract any sensitive information and make every good faith attempt to protect the privacy of any potentially affected individuals.