Originally published on January 25th, 2021
On September 26th, 2020 the WebsitePlanet research team in cooperation with Security Researcher Jeremiah Fowler discovered a non-password protected database that contained over 323,277 court related records. Upon further investigation we noticed that the records were all related to Cook County, Illinois, the second most populous county in the United States after Los Angeles County.
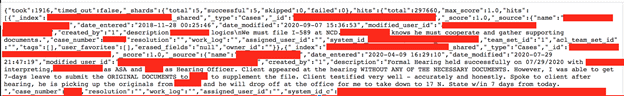
Nearly every record contained some form of personally identifiable information (PII) such as full names, home addresses, email addresses, case numbers, and private details about the cases. Based on the potentially sensitive PII exposed it was clear that this data was not meant to be public. This appeared to be an internal record management system that contained detailed notes about case status or about issues with the cases or individuals.
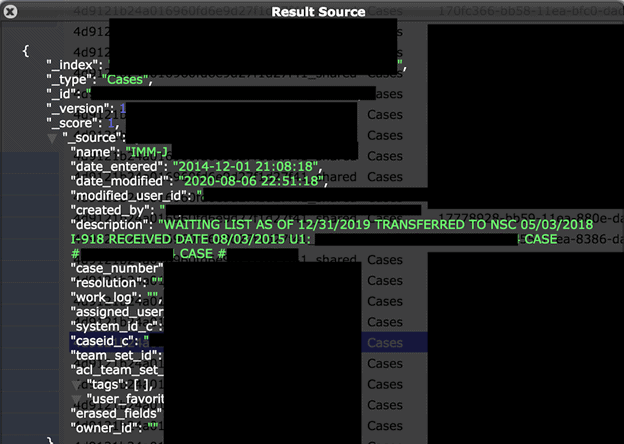
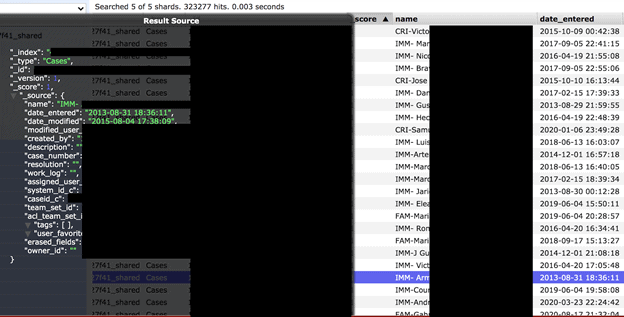
The records contained the names, addresses and very detailed case notes that exposed the plaintiffs and defendants and their cases in a tone that was clearly aimed for internal use only and should not have been publicly exposed. The court records dated back to 2012 all the way up to 2020. They were categorized by abbreviated names and I can assume that they were as follows: IMM (Immigration); FAM (Family); and CRI (Criminal). These records could have possibly been edited, altered, or even deleted due to the misconfiguration and lack of administrative credentials.
Once we understood what was at stake, we immediately sent a responsible disclosure notice to the Cook County Chief Technology Officer. Unfortunately, because we discovered the dataset on a Saturday, the data remained publicly exposed until Monday. It was secured and public access was restricted early Monday morning. We do not know how long the server had been left unsecured and exposed to anyone with an internet connection before we discovered the data and notified them.
Only Court Records
The database contained a total of 323,277 records that appeared to be unique. Usually there are configuration settings or logging details, but in this database it was only court records. Here is how the data was structured and appeared:
The Risk of Exposed Court Records
Immigration Court Records;
Immigration scams are a big business and prey on vulnerable people who are often navigating a system and laws they may not understand. Hypothetically, cyber criminals would have the case ID, dates, and enough confidential information from the leaked internal notes to easily scam these individuals. The leak exposed notes beside some of the email addresses indicating that “THIS IS THE EMAIL FOR CLIENT’S USCIS ACCOUNT”. The USCIS accounts are used for Citizenship and Immigration Services. Targeted social engineering is among the most dangerous kinds of threat these people are exposed to because it uses a relationship of trust combined with privileged data. This database would have been a gold mine of potential targets for a targeted campaign.
The US Federal Trade Commission (FTC) has outlined the most common tactics scammers use to target immigrants and how to avoid being a victim. These include scammers threatening deportation or requesting original documents, like a birth certificate or passport and holding them until a ransom is paid. Selling application documents that are usually provided for free is another common tactic. Immigration scams not only pose a financial risk but they could create serious problems in the applicant’s immigration status or even become a victim of identity theft. In this exposure there was a treasure trove of contacts and data that could have potentially been exploited for a wide range of nefarious purposes. Immigrants are in a vulnerable position and these are real threats against people who can rarely protect themselves or fight back for their rights due to lack of resources, including financial resources.
It is unclear if the affected individuals were notified about the data exposure or if they were informed about the risk of how this information could be used to potentially target them. We could not find any reference to a public notice of a data breach of court records. No one replied to our responsible disclosure notice, phone voice message, or a follow up email, so we were unable to know exactly what these records were used for or the full extent of the exposure.
The tone and details of the notes seem to deal primarily with the immigrant community. Some records were marked with the label “English Speaker” or “Non-English Speaker”. There is a very large and vibrant immigrant community from around the world in Cook County. According to the 2010 census Hispanics and Latinos (of any race) made up 24% of Cook County’s population. It would logically make sense that the court would provide assistance to those individuals who need it or do not speak English. Unfortunately, because no one responded to the data exposure notice we can only assume that this was a specialized department or case workers within the Cook County Court that assisted those who did not speak english or needed some type of help from the court.
As an example of how detailed the records were, one sampling read “I-30 (petition for Alien Relative) is approved through child\ she needs to marry in order to proceed with waiver\ Husband. However, Husband was accused of sexual assault against a minor. Need to wait to see Dispo of that charge to ensure eligibility – we will wait.” The file also exposed the name and case number of the individual in plain text. There were countless case notes that exposed the status or progress, if clients showed up to court unprepared without any documents, who needed a translator, and much more.
Family Court Records;
The danger of these records being exposed is that they can include records on children who may have been victims or juveniles who have committed a crime. These types of records could be highly sensitive and crime or abuse victims almost always have their identities protected. According to the Cook County Circuit Court’s website; “The Family Law Bureau includes the following areas: Domestic Relations Division which includes Divorce, Child Custody, Visitation and Domestic Violence; Child Protection Division which handles protecting minors from abuse and/or neglect; Juvenile Justice Division which handles crimes by minors”. The sensitive nature of many family related cases could allow risks including blackmailing families that private information would be leaked if they did not pay a ransom. These threats would be highly effective on people who might already be under a lot of pressure.
Criminal Court Records;
Similar to immigration records, these individuals could be targeted for their personal data. Identity theft can affect anyone and once criminals have this information they could apply for credit cards, loans, or fraudulent tax returns in the victim’s name.
Many types of court records in the US are public, but they lack specific details and offer only general information. Exposing ongoing cases or instances of sexual assault carries the potential risk of compromising the court proceedings and revealing the identities of the victims. Consequently, these individuals may become targets for blackmail, harassment, and threats aimed at disclosing their confidential court records.
Prime Target Left Exposed
State and local governments were the target of 45% of all ransomware attacks in 2020. Cook County is also home to Chicago, the 3rd largest city in the United States and home to more than 5.1 million people according to the 2010 census. This would make any Cook County data a highly valuable prize for cyber criminals. In this case there was no password needed and no security protections for the 323,277 records left wide open for anyone to see.
There have been several high profile data exposures of private companies that affected Cook County residents in the last few years including a large Hospital data breach. However, this appears to be the largest breach of Cook County internal records to date. We hope our discovery and notification helped protect and secure this sensitive data before it could be stolen, encrypted with ransomware, or wiped out by an automated bot script. Companies, organizations, and even governments must do more to protect the data they collect and store.