A Nigerian government healthcare agency’s unsecured buckets exposed thousands of applicants’ personal data
| Company name and location: | PLASCHEMA (Plateau State Contributory Health Care Management Agency), based in Nigeria |
| Size (in GB and amount of records/files): | Around 45GB, totaling over 75,000 files |
| Data Storage Format: | AWS S3 bucket |
| Countries Affected: | Nigeria – citizens of Plateau state |
A data breach affecting the Nigerian organization PLASCHEMA (Plateau State Contributory Health Care Management Agency) exposed the personal data of thousands of citizens, according to the findings of the Website Planet research team.
PLASCHEMA manages Plateau State Universal Health Care, a program designed to bring affordable healthcare to Plateau State, a region in Central Nigeria.
11 of PLASCHEMA’s buckets were left unsecured without any authentication or encryption controls in place. As such, the organization’s buckets exposed over 75,000 files totaling around 45GB of data.
Each unsecured bucket contained PII belonging to program applicants from a different city located in Plateau State.
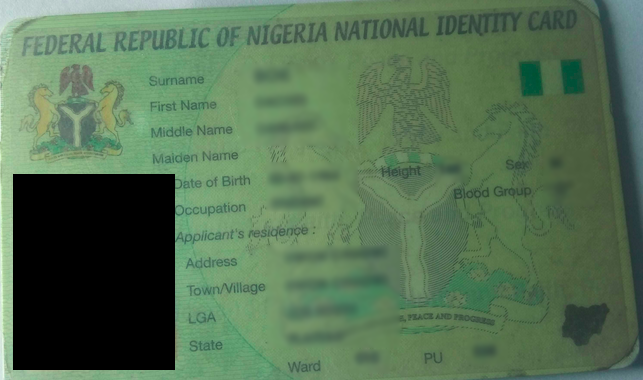
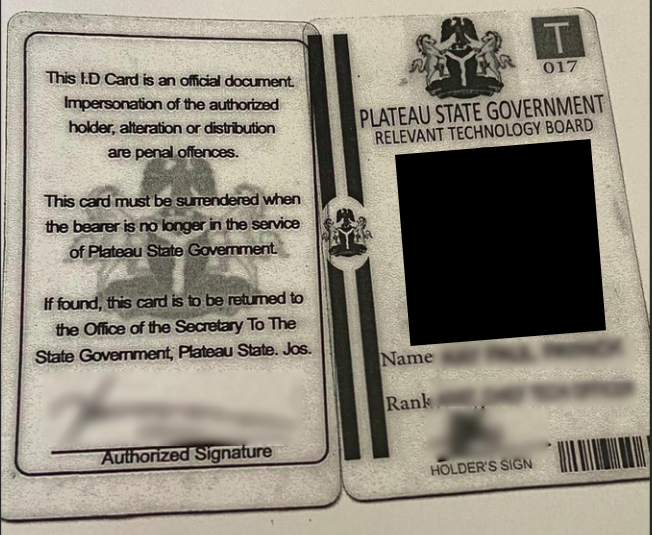
Among other files, the open buckets contained ID cards that exposed a range of applicant PII. Based on the volume of these files, we estimate that over 37,000 people are affected by PLASCHEMA’s data incident.
Website Planet researchers discovered PLASCHEMA’s buckets, left in open form, without any encryption or password protection, as part of our extensive web mapping project. We use web scanners to identify unsecured data stores on the internet. We responsibly analyze, secure, and report these data incidents to raise awareness about the dangers of cybercrime and help affected companies and users.
Status of the Data Exposure
We found PLASCHEMA’s open bucket on April 3rd, 2022.
- April 5th, 2022: We messaged the Nigerian government.
- April 11th, 2022: We sent follow-up messages to previous contacts and contacted the Nigerian CERT.
- April 14th, 2022: We sent more follow-up messages to previous contacts and the Nigerian CERT.
- April 15th, 2022: We messaged AWS regarding the breach.
- April 25th, 2022: We contacted the Nigerian CERT via Twitter.
- April 26th, 2022 – May 2nd, 2022: We sent several follow-up messages to different Nigerian CERT addresses and received two auto-replies.
- May 10th, 2022: We contacted the Nigerian CERT via Twitter again and they responded, asking for more information.
- May 11th, 2022: We responsibly disclosed the incident to the Nigerian CERT. We also emailed Nigeria’s Data Protection Officer.
- May 12th, 2022: The Nigerian CERT responded to our message, saying “We will ensure the incident is resolved as soon as possible.”
- May 25th, 2022: We contacted the Nigerian CERT again since the buckets were still unsecured.
- May 30th, 2022: The Nigerian CERT responded to our message, saying they suffered a setback while trying to contact PLASCHEMA, but that they had sent a hardcopy letter to the organization.
- Jun 09th, 2022: Contacted the Nigerian CERT again, since the buckets were unsecured. They replied that same day, telling us that they contacted the organization hoping that they would secure the buckets.
- Jul 20th, 2022: All buckets secured.
Customer Data Exposed
- Applicants’ PII: Identity documents containing full names, dates of birth, height, sex, occupation, blood group, address, state, town/village, local government area, place of birth, parents’ full names, registration details, etc.
- Applicant photos: Identification photos of citizens applying to PLASCHEMA’s program.
Files dated from January 20th, 2021 until date on PLASCHEMA’s open buckets, which were live and being regularly updated at the time of discovery.
Amazon is not responsible for PLASCHEMA’s data exposure.
Identity documents consisted of applicants’ ID cards and birth certificates with each of these files exposing some different forms of data.
Identification photos, which showed applicants’ faces, also featured heavily on the buckets. In some cases, identification photos showed children’s faces. Presumably, exposed children are related to program applicants, and each one is included in their family’s health plan application.
We found over 37,000 examples of each file type (identity documents and identification photos) on PLASCHEMA’s buckets.
You can see evidence of a birth certificate and an identification photo below.


Impact on Applicants and PLASCHEMA
We do not and cannot know whether malicious actors have accessed PLASCHEMA’s open buckets. However, if hackers have accessed the buckets, they could target citizens with cybercrimes after obtaining their data.
- Impersonation: Hackers could impersonate affected applicants online with IDs, PII, and headshots exposed. Many online services accept these documents as proof of identification. Hackers could use this information to join online services in victims’ names and conduct illegal activities and communications.
- Reputational damage: PLASCHEMA’s program is extremely important for Plateau State citizens, especially those from impoverished communities who lack access to proper healthcare. PLASCHEMA’s data exposure could ultimately damage residents’ confidence in the organization’s healthcare program.
Much of the buckets’ exposed data is unchangeable, which potentially heightens the impact of this data incident.
PLASCHEMA could come under the investigation of Nigeria’s data protection authority, the National Information Technology Development Agency (NITDA), if it has exposed citizens’ personal data.
The NITDA can impose a maximum fine equivalent to 2% of the guilty company’s annual turnover or 10 million Naira (whichever is greater) for a data breach.
Protecting Your Data
Affected Plateau State citizens should monitor social media and other popular sites and services for fake accounts in their names.
About PLASCHEMA
Quality healthcare was once a luxury afforded to only the most privileged Nigerian citizens. Now, PLASCHEMA’s program is making professional healthcare accessible to a much broader demographic.
PLASCHEMA’s Plateau State Universal Health Care program sets out with the mandate “to ensure access to affordable, equitable, timely and quality healthcare” for Plateau State residents “irrespective of their socioeconomic status.”
Citizens apply for the scheme and pay an affordable subscription fee, after which members can purchase medication at a massively reduced cost.
We know PLASCHEMA owns the buckets as the organization’s logos regularly appear throughout each bucket’s contents. As listed in the AWS access lists, the same owner operates all 11 buckets.

How and Why We Report on Data Breaches
We want to help our readers stay safe when using any website or online product.
Unfortunately, most data breaches are never discovered or reported by the companies responsible. So, we decided to do the work and find the vulnerabilities putting people at risk.
We follow the principles of ethical hacking and stay within the law. We only investigate open, unprotected databases that we find randomly, and we never target specific companies.
By reporting these leaks, we hope to make the internet safer for everyone.
What is Website Planet?
Website Planet prioritizes honesty and serves as the top resource for web designers, digital marketers, developers, and businesses with an online presence. We offer tools and resources catering to individuals ranging from beginners to experts.
We have an experienced team of ethical security research experts who uncover and disclose serious data leaks as part of a free service for the online community at large. Our recent discoveries include a breach at a famous US news corporation, and an incident that exposed millions of website users’ online traffic.
You can read about how we tested five popular web hosts to see how easily hackable they are here.