Security researcher Jeremiah Fowler together with the Website Planet research team discovered an open and non-password protected database that contained 12,976,279 records. The total size of the dataset was 58 GB and contained content management data, including employees PIIs. Upon further research nearly all records contained information indicating FOX content, storage information, internal FOX emails, usernames, employee ID numbers, affiliate station information and more. One folder contained 65k names of celebrities, cast and production crew members and their internal FOX ID reference numbers. The records also captured a wide range of data points including event logging, host names, host account numbers, IP addresses, interface, device data, and much more.
Many of the records were labeled “prod” and this is usually an abbreviation for production or live records. We immediately sent a responsible disclosure notice and public access was restricted shortly after. The environment was listed as “CMS” and we did not see any references to test or demo inside the records.
Simply put, a content management system helps an organization to manage digital content. As the massive number of documents indicates, an organization as large as FOX requires a complex and sophisticated content management system. The digital asset management database shows a detailed look at the internal collaborative environment divided by users, administrators, and content.
What the database contained:
- Total Size: 58.03 GB
- Total Docs: 12,976,279
- Many references to “theplatform” and links that redirect to Comcast Technology Solutions and all of the content was FOX related. (ThePlatform is an online video management platform that manages, monetizes, and syndicates video views for media companies).
- Internal CMS records of FOX that exposes user IDs, event logging, host names, IPs, interface and device data. Many of the records are labeled Production.
- Large number of email addresses of users including 701 internal @fox.com email addresses that could be at risk of a targeted phishing campaign. These emails also include internal ID numbers and security or user roles.
- The files also show where data is stored, content delivery paths, and served as a virtual blueprint of how the network operates from the backend. There were also links to FTP (File Transfer Protocol) and content storage locations.
- The non-password protected and unencrypted database was at risk of a ransomware attack that would encrypt the data. The exposed environment is marked as “CMS” and could allow cyber criminals to insert malicious code or identify vulnerabilities for a future cyber attack.
The indices show the type of data collected and stored. The folders contained descriptions or abbreviations of how the records were filtered. There were a total of 102 folders with titles such as user roles, users-publisher, users_v2, video-publisher, dcc-person-data, and other content related names.
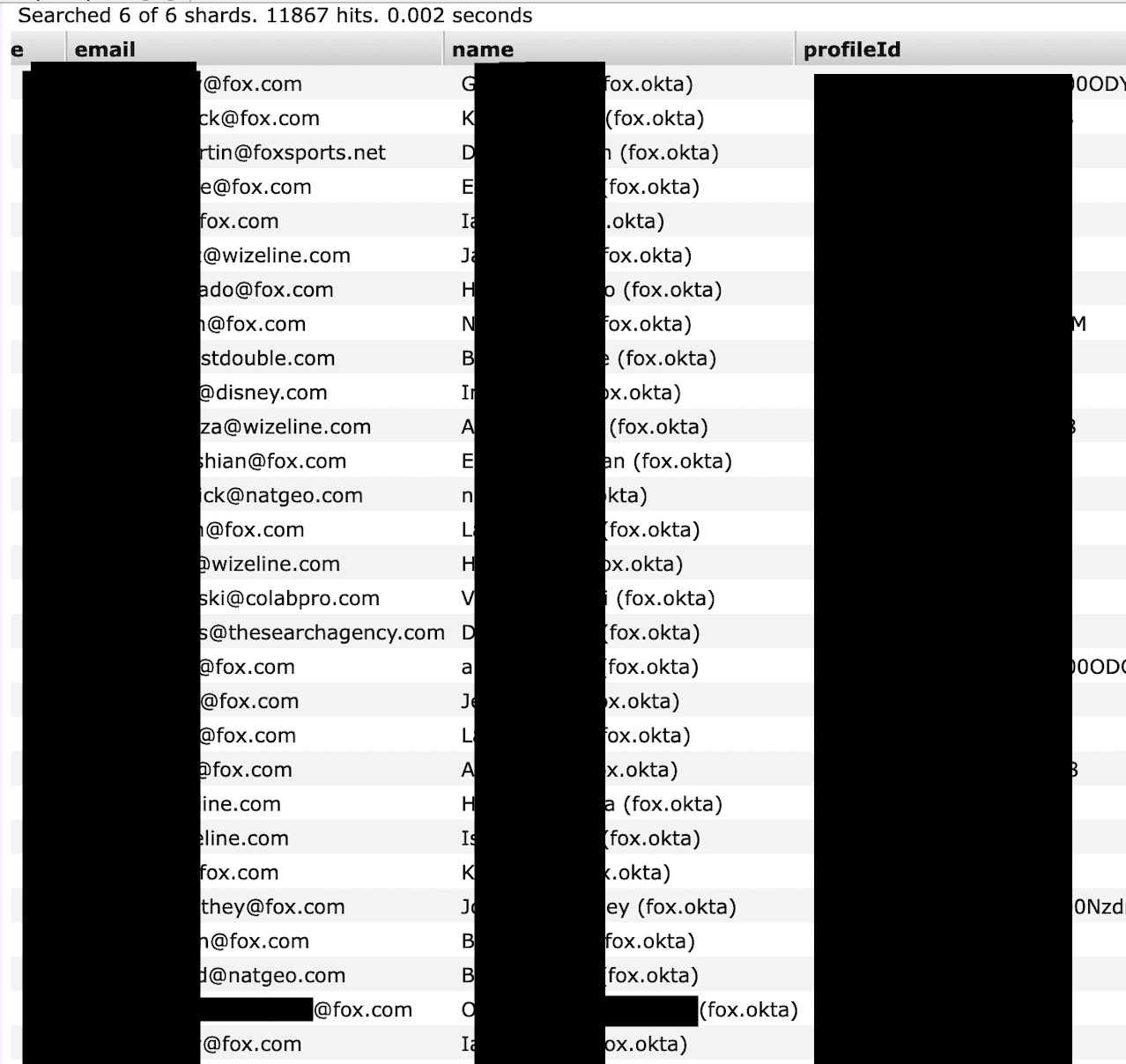
How the email accounts appeared in the database. There were numerous other email accounts including 700+ internal @Fox accounts.
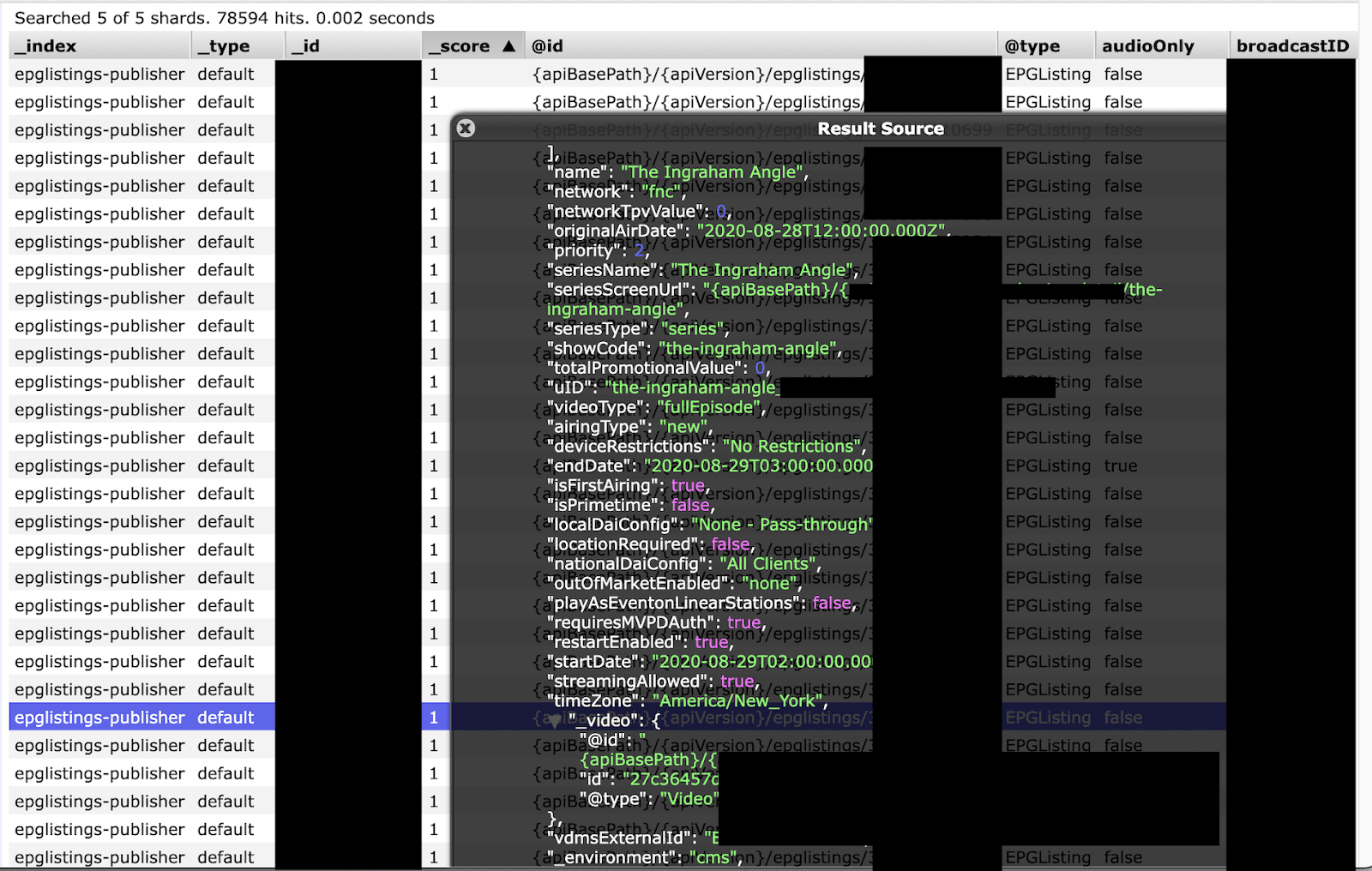
Detailed view of how the records showed what information was collected on FOX programs and logging information about individual episodes, API data, storage location, Internal and external IDs and more.
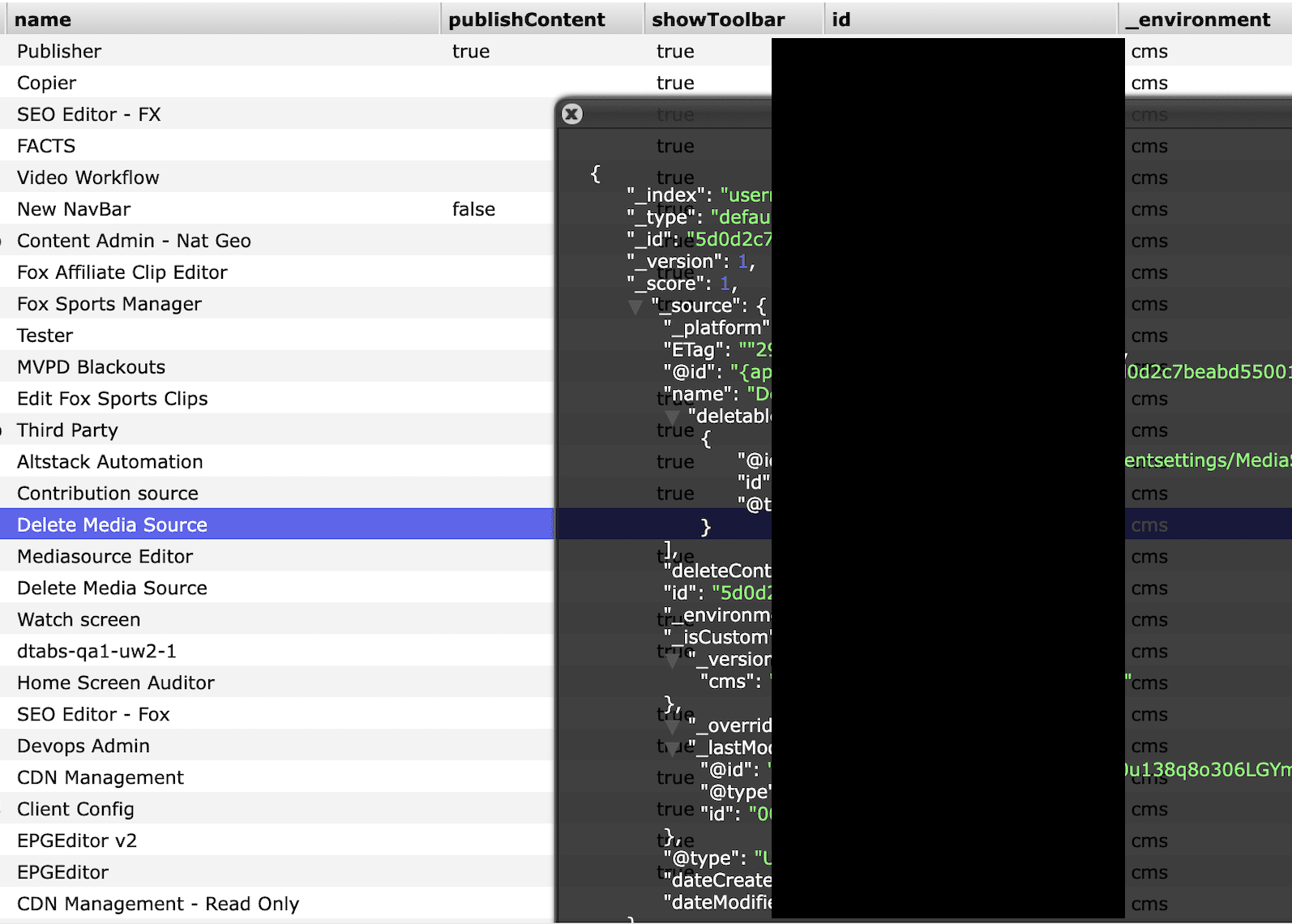
An example of user roles and what privileges they would have inside the CMS system. This would indicate what users could publish, edit, or delete content and how these actions are listed and identified.
The Fox Security Team replied:
“Thank you again for sharing your observations. As a follow up to our email yesterday, we have continued to investigate and we have determined that the database referenced in your email is a development environment not connected to any production environment. The ability to publicly access such database has been addressed. As part of our investigation, we are reviewing logs to determine any anonymous access to the database.”.
As a security researcher it is not our duty to question or dispute if a database is a specific environment such as production or development. We only report on what the database contained, who owned the data, and then provide real world examples of how this data could be a potential security risk. We were able to validate that a sampling of emails and users’ names were real individuals and FOX employees.
There were many references to Comcast Technology Solutions inside the data. We initially suspected that these records might have been managed by Comcast and they were responsible for the data leak. We reached out to their security team and they confirmed that Comcast did not manage this dataset and that it likely belonged to a customer that was using their services, but would not identify who the customer was. Comcast offers metadata management for the entertainment industry and there was recently a case study published titled “A Metadata Makeover for FOX”
This publicly accessible dataset offers a comprehensive behind-the-scenes view of how FOX delivers its content, along with a detailed list of criteria employed to manage the data. This encompasses factors such as content format, delivery channel, revenue sources like advertising, subscriptions, or free access, and various other pertinent details.
The dangers of this type of exposure
Often development environments mirror live production environments and use the same storage repositories, middleware, and infrastructure. In this case anyone with an internet connection had access to these records, and what appeared to be real internal user data, and some form of CMS system. This would also serve as valuable information for cyber criminals to identify potential vulnerabilities or an attack vector once they know the IPs, urls, account numbers, individuals with administrative credentials, and software applications used by FOX.
Development environments that contain real data sometimes can unintentionally create a range of cyber security risks. Employee email addresses pose threats from a targeted phishing campaign to long term social engineering attacks. Hypothetically cyber criminals could see who has administrative rights and try to gain access to their accounts and any additional password protected assets. They can reference internal information that only employees would know to build a relationship of trust. One way to mitigate this risk would be to enable 2 factor authentication or other additional security measures.
It is not out of the realm of possibilities that a Nation State or authoritarian regime would target a news organization to identify whistleblowers or target investigative journalists. This is a real threat that members of the media and news organizations face on a daily basis. One of the most notorious cases targeting journalists was the military grade Pegasus spyware. The malicious link can be sent by email or as an SMS and the victim in some cases would not even need to touch their device to be infected using a “zero-click” delivery method. We are not indicating FOX Journalists were targeted or at risk and only raise the possibility based on a real history of cyber threats targeting journalists and members of the media.
Any non-password protected database could potentially allow someone to insert malicious code into the network. Criminals or state actors would hypothetically have a working blueprint of the content infrastructure and easily identify what 3rd party software versions and builds are being used. They could also see if the software is unpatched, outdated, or not using the latest versions. Once they have this information in theory they can look for known exploits and try to gain access using a backdoor or other attack vector. It is a well known fact in the security community that development environments in general often lack proper security protections to protect against a targeted cyber attack.
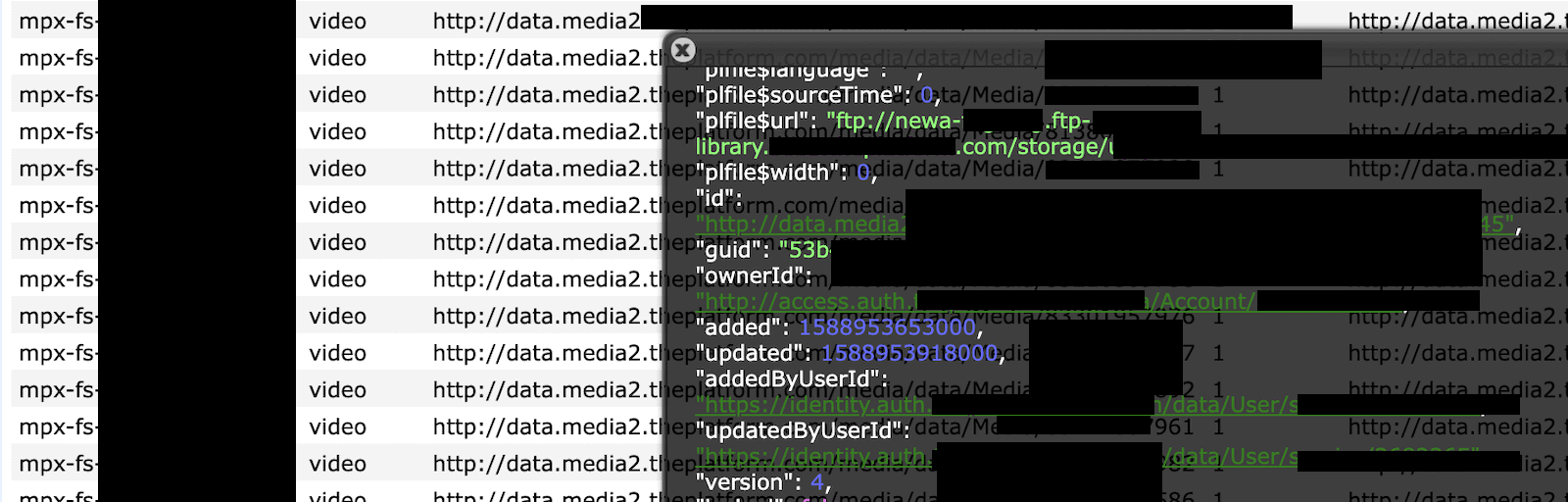
Example of FTP, access auth, and user ID number how it appeared in the database.
Identifying the location of FTP urls, directories, and folders also presents a potential risk. FTP stands for File Transfer Protocol and allows files to be transferred between computers. Unfortunately, FTP is an almost 50 year old technology and was not designed to be secure or withstand the modern threat landscape. Many in the security community consider FTP to be an insecure protocol and the information can be at risk of being targeted for brute force attacks, data sniffing, credential spoofing and other lowtec methods. Another potential security vulnerability with FTP is that the authentication method uses plain text usernames and passwords that are unencrypted making the data potentially vulnerable.
The FOX Security Team acted fast and professionally to close access to the unsecured and publicly exposed database. It is unclear how long these records were exposed or who else may have had access to the dataset. As security researchers we never extract or download the data we find and only take a limited number of screenshots for validation purposes. We are not implying any wrongdoing by FOX, Comcast Technology Solutions or their partners. Nor, are we implying that any customer or user data was at risk.
We are only highlighting our discovery to raise awareness of the dangers and cyber security vulnerabilities posed by misconfigured databases, publicly exposed internal records, and how that data is stored. We advise any company or organization that has a data incident that affects any environment that uses real data to consider changing administrative and user credentials. It is always a good idea to encrypt sensitive data, enact cyber hygiene practices, and conduct penetration testing often.
In full transparency we want to include that FOX claims this was a general company development environment, not a production environment. We also confirm that there were no external customer records. Of course data describing video assets – e.g., the bios of actors, directors, writers, program titles, character descriptions, etc. associated with various series is publicly available information. The focus of the report is on our discovery of a non password protected database, content management security, and possible or hypothetical risks associated with this type of exposure. When we find an exposed dataset we report on; what was found, who owned it, and what are the potential real world cyber security risks associated. We included in the report FOX’s reply to the initial responsible disclosure notice and added the disclaimer that, it is never up to us to dispute their claims if the data was production or development or otherwise. What we do report on is the fact that many development environments mirror production environments and can use the same software, middleware, sometimes real data, file names, and data storage locations.
It is a fact that up to 65% of active cyber crime groups relied on spear phishing as the primary infection vector and I was unable to find any list of 700+/- FOX employee names and emails in any publically available list online using a search engine. We confirm that no credentials were exposed in plain text, but exposed employee names, emails, internal usernames or ID numbers could be considered by some to be partial credentials if they are used in FOX’s admin process. Metadata can provide puzzle pieces of information that should not be publicly exposed to anyone with an internet connection. Our goal is to highlight risks, raise awareness, and promote proper cyber security hygiene for educational purposes.