Dodo Point’s open Amazon bucket exposed at least 1 million customers’ PII and thousands of retail outlets’ sensitive data.
| Company name and location | Dodo Point, operated by Yanolja Cloud, based in Seoul, South Korea |
| Size (in GB and amount of files) | Over 38 GB of data, around 73,000 files |
| Data Storage Format | Amazon AWS S3 bucket |
| Countries Affected | South Korea |
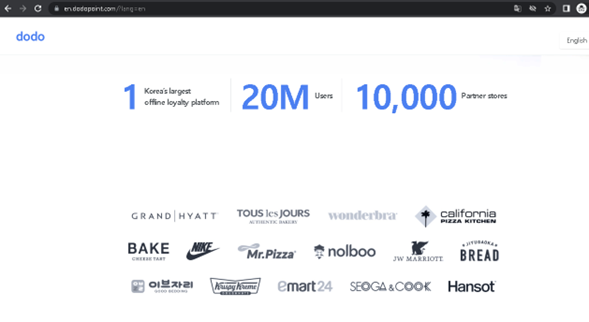
A trove of customer PII and sensitive company information has been exposed in an incident affecting Dodo Point, a South Korean “loyalty platform” solution for retail outlets such as cafes, restaurants, beauty salons, and more.
The company’s Amazon bucket was left unsecured, without any encryption or password-protection controls in place. As a result, the bucket exposed over 38 GB of data totaling around 73,000 files.
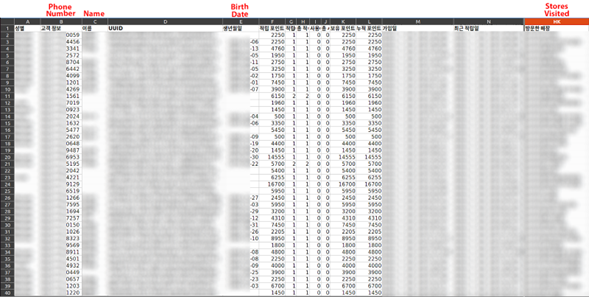
Website Planet researchers found that the number of customer records in each excel file was proportional to the file’s size. In other words, we knew that “X MB of data” could potentially expose “X amount of customer records” in our sample files. By applying this calculation to all 38+ GB of data, we can estimate that the bucket contained around 8 million customer records. Considering the proportion of duplicate entries in the files we analyzed for our research, we believe at least 1 million unique customers and over 5,000 stores are affected across the entire bucket.
The affected stores are Dodo Point’s clients and affected customers were shopping at retail sites using Dodo Point’s solution.
Dodo Point provides each client store with an app on a point-of-sale device. Customers can use the device to sign up for a store’s loyalty program — which is an initiative designed to reward shoppers for their continued purchases. Dodo Point’s solution updates retail customers about their earned benefits and offers via text.
According to the company’s website, huge multinational brands, including Nike and JW Marriot, use Dodo Point, which is owned by the Seoul-based company Yanolja Cloud.
Customer loyalty programs collect a wealth of information about shoppers and their buying habits, as Dodo Point’s bucket demonstrates. Customers should consider this extensive data collection and its associated privacy risks before joining a loyalty program.
Website Planet researchers discovered this store of information, left in open form, as part of our extensive web mapping project. We use web scanners to identify unsecured data stores on the internet. We responsibly analyze, secure, and report these data incidents to raise awareness about the dangers of cybercrime and help affected companies and users.
Status of the Data Exposure
We found Dodo Point’s open bucket on March 28th, 2022.
- March 28th, 2022: We contacted Spoqa — the company that owned Dodo Point before Yanolja Cloud — in an attempt to responsibly disclose the incident, but didn’t receive a response.
- April 5th, 2022: We reached out to new contacts at Spoqa (no response).
- April 15th, 2022: After initial contact, we responsibly disclosed the incident to the Korean CERT but received no further communications.
- April 15th, 2022: We responsibly disclosed Dodo Point’s incident to AWS (no response).
- April 26th and May 4th, 2022: We contacted new Spoqa (Dodo Point) contacts.
- May 8th, 2022: We reached out to Yanolja (new Dodo Point owner).
- May 9th, 2022: We responsibly disclosed the breach to Yanolja (Dodo Point) and the company promptly responded to our communications.
- May 11th, 2022: Dodo Point’s bucket was secured.
Yanolja Cloud acquired DodoPoint while we were attempting to disclose the breach to Spoqa. Yanolja acted quickly and professionally to close the breach as soon as we contacted them about the open bucket.
Customer & Company Data Exposed
Dodo Point’s bucket contained three datasets: Files with tables of customers’ personal information, Dodo Point clients’ monthly reports, and Dodo Point clients’ payment details.
These datasets exposed the personal and sensitive data of retail stores using Dodo Point’s services (clients) and retail customers who joined loyalty programs via Dodo Point.
Exposed data included:
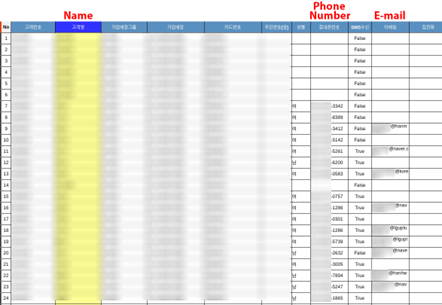
- Customers’ personal data: Names, dates of birth (of most customers), genders, phone numbers, email addresses (of some customers), store visited, date of joining the service, and reward points gained.
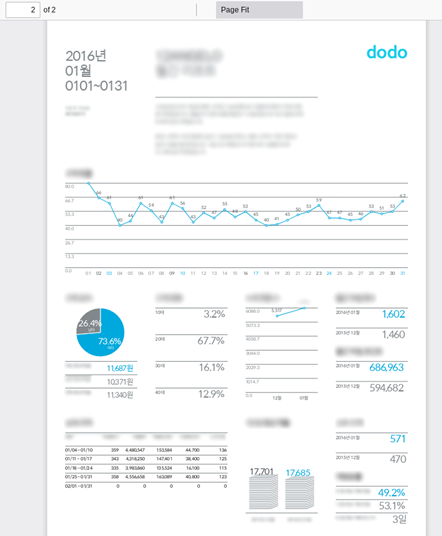
- Sensitive business data: Daily shop incomes, amount of new customers, avg. profit per customer, customer segmentation (by gender and age), and performance comparisons to previous months.
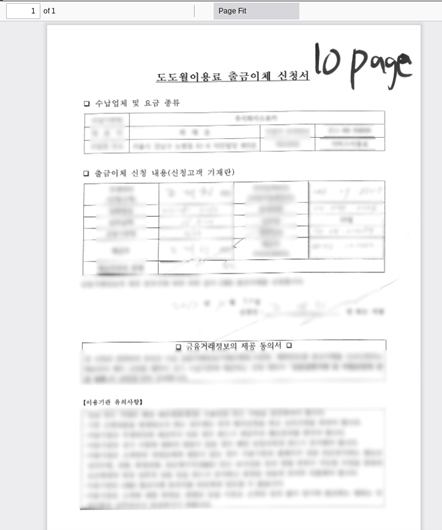
- Client payment details: Bank transfer and direct debit details.
Files on Dodo Point’s bucket dated from April 6th, 2012 to May 2022. The bucket was live and was being regularly updated at the time of discovery.
Amazon is not responsible for the misconfiguration of Dodo Point’s bucket.
An estimated 8 million total customer records were exposed in various .xls files on the bucket. Our estimate figure is based on a small sample of files and, as such, the true number of records could be higher.
Over 10,000 client reports — seemingly part of Dodo Point’s “Dodo Insights” service — and less than 1,000 payment details files exposed sensitive business information belonging to Dodo Point’s clients.
You can see examples of the bucket’s data below.
Impact on Customers and Dodo Point Clients
We do not and cannot know whether malicious actors have accessed Dodo Point’s open bucket. However, exposed customers and businesses could face several security risks if bad actors have obtained the data.
- Privacy violation: Customers are identifiable and have private information like “store visited” and “date of joining” exposed. This represents a privacy violation that could impact customers’ personal lives. For example, a customer could face consequences if their employer found out they visited a store during working hours. Furthermore, by linking phone numbers to people, someone could use the data to augment digital campaigns based on exposed information about users’ interests (e.g. fashion, electronics, etc).
- Phishing and scams: Attackers could send customers phishing messages and scams via phone or email, referencing personal information and shopping habits to trick victims into providing money, sensitive information, or downloading malware.
- Industrial espionage: Dodo Point clients have detailed reports containing revenues and customer traffic data exposed, not to mention their payment details. Rival businesses could use this information to gain insights into exposed businesses and achieve a competitive advantage.
Yanolja Cloud (the company that owns Dodo Point) could come under the scrutiny of South Korea’s Personal Information Protection Commission (PIPC). According to the Personal Information Protection Act (PIPA), any data controller that fails to properly secure data could face fines up to 20 million won (~$16,500) or imprisonment of no more than 2 years.
Protecting Your Data
Customers who’ve signed up to Dodo Point should ignore any messages from unknown or suspicious sources. Customers should refrain from clicking links in emails or SMS messages unless they’re 100% certain the source is legitimate. Businesses and individuals alike should educate themselves and their staff about scams, phishing attacks, and malware.
About Yanolja Cloud & Dodo Point
Yanolja Cloud is headquartered in Seoul, South Korea, and was founded in 2005. Yanolja acquired Dodo Point from Spoqa in late January 2022.
Dodo Point is a customer club solution that offers shoppers convenience and provides businesses with several added benefits.
Dodo Point updates customers about their rewards via text message, which means they don’t have to carry a loyalty card or download an app.
Businesses that purchase Dodo Point can make use of customer analysis features (“Dodo Insight”), marketing automation tools (“Dodo Message”), and targeted advertising functionality (“Dodo Ads”).
We know the bucket belongs to Dodo Point because pictures on the bucket also appear on Dodo’s website, while services listed on the company’s website match the bucket’s content.

How and Why We Report on Data Breaches
We want to help our readers stay safe when using any website or online product.
Unfortunately, most data breaches are never discovered or reported by the companies responsible. So, we decided to do the work and find the vulnerabilities putting people at risk.
We adhere to ethical hacking principles and operate within the boundaries of the law. Our investigations solely involve randomly discovered, open, and unprotected databases, and we never focus on specific companies.
By reporting these leaks, we hope to make the internet safer for everyone.
What is Website Planet?
Website Planet is the number one resource for web designers, digital marketers, developers, and businesses with an online presence. You’ll find tools and resources for everyone, from beginners to experts — and honesty is our top priority.
We have an experienced team of ethical security research experts who uncover and disclose serious data leaks as part of a free service for the online community at large. Our recent reports include a breach at a major US news corporation and an incident that exposed millions of websites users’ online traffic.
You can read about how we tested five popular web hosts to see how easily hackable they are here.