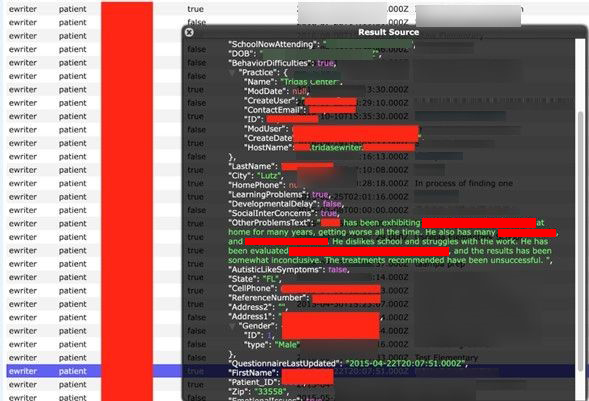
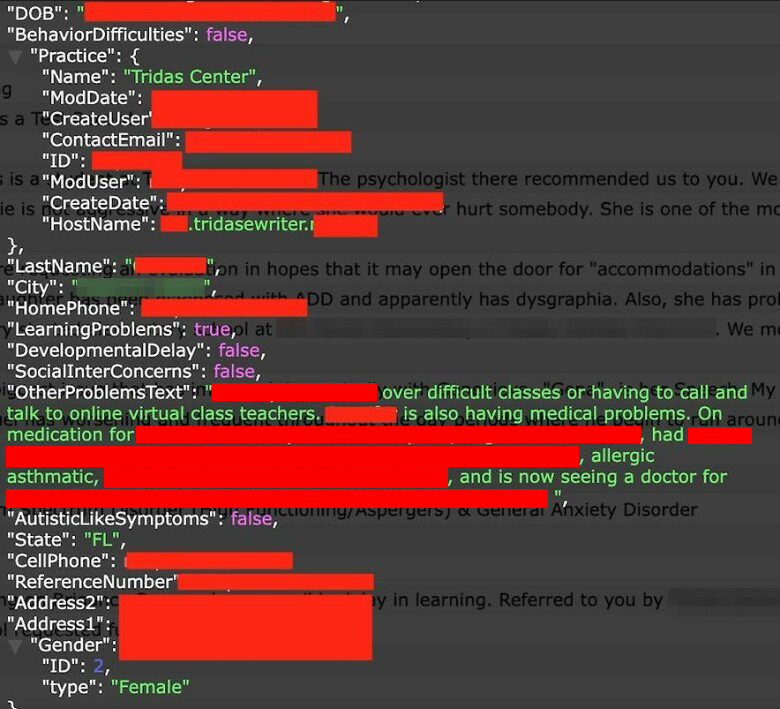
Security researcher Jeremiah Fowler together with the Website Planet research team discovered an open and non-password protected database that contained over 16,000 records. A limited sampling of 1,000 records was reviewed to identify who owned this data and notify them that sensitive information was exposed. Each record reviewed contained some form of personally identifiable information (PII) of children. The records appeared to be unique based on the Patient ID number. These included their names, date of birth, Patient ID number, home address, school attended, special needs, medical diagnoses, behavioral or social problems, and more data that appears to be recent.
Upon further research references to Tridas eWriter, an online interview system operated by the Tridas Group LLC, were found. The Tridas Group LLC offers software that works with schools and parents to facilitate the diagnosis and management of children with ADHD, Autism, learning challenges, and other disorders or common conditions. The findings appeared to be a collection of records from Tridas eWriter questionnaires completed by parents, which the Tridas Center (where assessments of children would take place) suggested should be completed before the first evaluation appointment. We note that, according to the Tridas Center website, the Tridas Center closed on December, 31 2019. We immediately sent a responsible disclosure notice to the Tridas Group LLC and public access was restricted shortly after.
According to their website: “Tridas eWriter brings together experts in child development and behavior along with experts in technology to create a groundbreaking Internet based application. Tridas eWriter provides secure, HIPAA compliant online questionnaires and it generates a detailed report that organizes the data in an easy-to-read format to facilitate the diagnosis and management of these complex challenges”.
The children were categorized with tags such as: Attention Difficulties, Behavior Difficulties, Autistic Like Symptoms, Emotional Issues, Learning Problems, Social Inter Concerns, Developmental Delay, and others.
The most surprising part of the discovery was that these records appeared to include the parent’s summary or a questionnaire of their child’s condition. They were very detailed, some painted a complete picture of the child’s challenges, and in many cases, there were stories or situations to validate why they believed their child needed assistance. This information, once shared on the platform, should have only been made accessible to medical professionals.
The data was, however, publicly accessible through a misconfigured IP that showed the host domain, login portal, and where the data was stored. Any potential exposure of medical or health records has a range of risks that could impact families and children.
The database included the following:
- Total Records Exposed: Over 16,000
- Internal records of questionnaires completed by parents that include thechildren’s first and last names, date of birth, physical address, name of the school they attend, parent’s phone number, and detailed physical or mental health information that should not have been publicly exposed. These notes provide profiles of the children’s issues or challenges including medical diagnosis, medicine prescribed, learning disabilities, violence, abuse, or other issues.
- Our findings were validated using a limited sampling of names that appear to be real people who share the same surname as individuals living at the addresses listed in the records according to publicly available resources.
The exposed individuals and users could be targeted for medical extortion, social engineering scams or phishing attacks based on exposed personal information, should any ill-intentioned hacker have discovered the database before it was secured. However, we cannot and do not know whether such hackers did so.
A ransomware attack could have jeopardized the non-password-protected database, potentially encrypting its data. Cybercriminals could have exploited the exposed environment to insert malicious code or identify vulnerabilities for a future cyber-attack.
Medical History Extortion
Hospitals and doctors’ offices have been targeted in the last several years in ransomware attacks where highly sensitive medical records are encrypted and cybercriminals demand a ransom payment for restoring the data. Non-password-protected records are also an easy target for a different threat where unethical hacker groups or criminals could threaten to publicly expose or leak sensitive information online if they do not receive an extortion payment. We are not implying this is the case with these records, we are only highlighting potential risks.
It has been estimated that upwards of 90% of all cyber attacks have some type of social engineering component making this a serious risk to individuals who have had their personal or medical information leaked. Data extortion occurs in an estimated 70 percent of all ransomware attacks.
When there is a data breach of financial data, people can take many steps to repair their credit history, but health data presents different challenges as potentially including personal and sensitive information on longstanding conditions. The information in these records, as pertaining to children, could potentially follow them around for the rest of their lives if it were dumped online or on the dark web.
Health data is a treasure trove for criminals and records can sell for up to $1,000 on the dark web depending on the information they contain. There the average cost of a credit card record is $10 while a social security number (SSN) costs only $4 to buy. Medical data is highly valuable and sought after by criminals. Medical technology companies that collect and store patient data must do more to protect the data they collect. We always recommend that sensitive data should be encrypted and regular penetration testing should be conducted to identify vulnerabilities on network systems.
Children’s Data Matters
It appeared that some of the records could fall under Health Insurance Portability and Accountability Act of 1996 (HIPAA) regulations by revealing detailed information about health issues, medical procedures, medication prescribed, and more. HIPAA regulates individuals’ legal rights over their medical data and who can share or access that medical data. Children with special needs or other challenges, like many of those whose records were exposed, are particularly vulnerable and deserve their personal or health information to be fully protected in line with applicable laws. Data collection and digital records are now the core foundation of many health, education, and social services. Patients are, however, often unaware of where the information they provide will be stored or what security practices will be used to keep these records safe.
A majority of the children were located in the US state of Florida. As responsible members of the security community we did not download or extract any data, only took a limited number of screenshots to validate our findings, and reported our discovery to the Tridas Group LLC immediately. We are not implying any wrongdoing by the Tridas Group LLC or their partners and we only highlight what we found, who owns the data, and give real-world examples of how that information could be exploited. We publish our findings to increase cybersecurity awareness and in cases where sensitive or vulnerable individuals have been potentially exposed. It is always a good idea to encrypt sensitive data, enact cyber hygiene practices, and conduct penetration testing often.
It is unclear how long the database was exposed or who else may have had access to these records. It is also unknown if affected individuals have been notified as required under the Florida Information Protection Act of 2014 or other applicable laws. The Florida Information Protection Act was passed to better protect Floridians’ personal information by ensuring that businesses and government entities take reasonable measures to protect personal information and report data breaches to affected consumers. We did not see any indication that this was test data or dummy records and at the time of publication, we have not received a reply to our responsible disclosure notice.