Company name and location: Credinet.co / Sistecredito, based in Colombia
Size: Around 100 MB of data, totaling 143,876 records
Data Storage Format: Elasticsearch
Countries Affected: Colombia
The Website Planet research team can reveal a significant data leak affected Credinet, a credit platform owned by the Colombian financial company Sistecredito.
Sistecredito provides hire-purchase financing options for customers looking to buy goods now and pay later in different affiliated establishments across the country. The Credinet platform is used by retail outlets that want to sign customers up to the Sistecredito service, to finance the purchase of goods that are sold in-store.
Credinet/Sistecredito stored hundreds of thousands of records on an unencrypted and not password-protected Elasticsearch database. The server contained sensitive forms of data that could be used by hackers to place thousands of people at serious risk of cybercrime.
Customer Data Leaked
Credinet/Sistecredito stored various forms of data on a misconfigured Elasticsearch server, which was being used without any password protection. As a result, the Credinet platform has leaked a total of 100MB of data, which equates to 143,876 records.
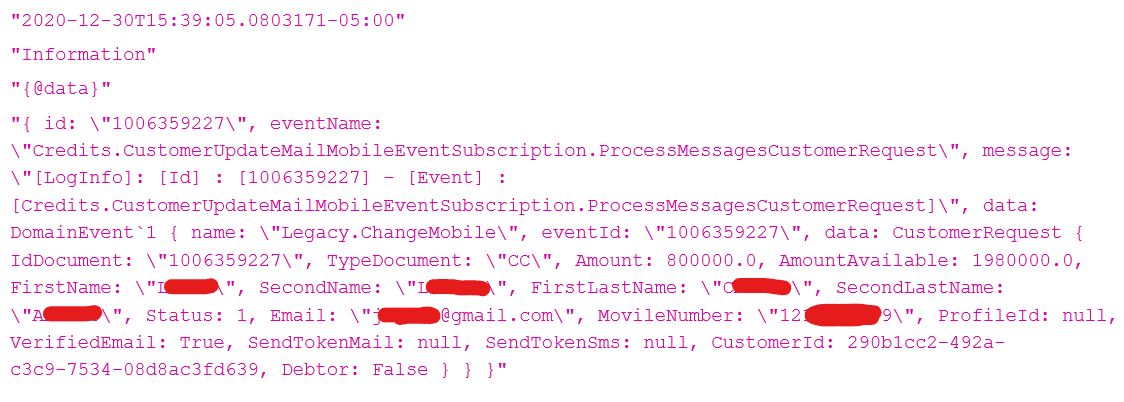
Exposed data affecting Credinet/Sistecredito customers includes:
- Customer PII: Logs containing names, surnames, email addresses, mobile phone numbers, along with financial data.
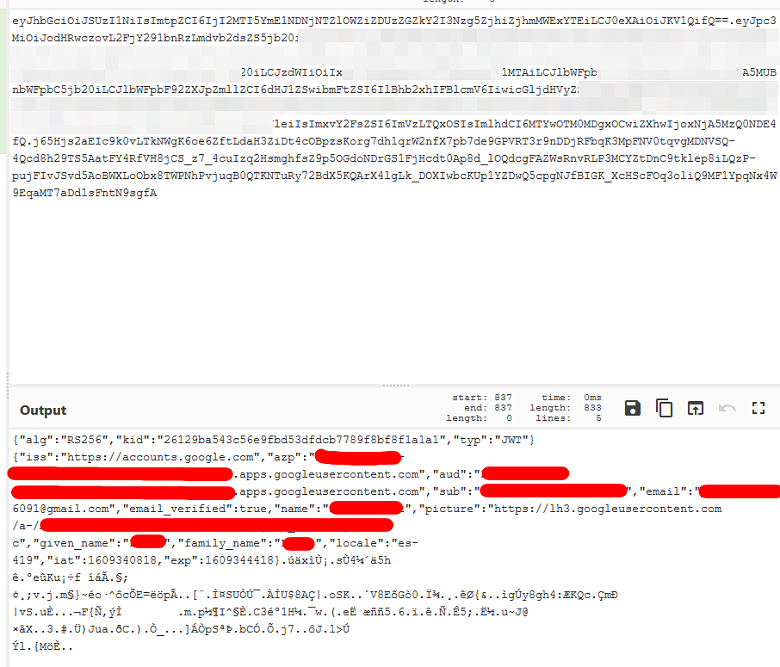
- JWT tokens: Around 3000 leaked records contained ‘JWT tokens.’ These can be used to generate ‘access tokens’ that authenticate as Credinet users, providing hackers entry to customer accounts. Most of the leaked files containing JWT Tokens also contain customer email addresses.
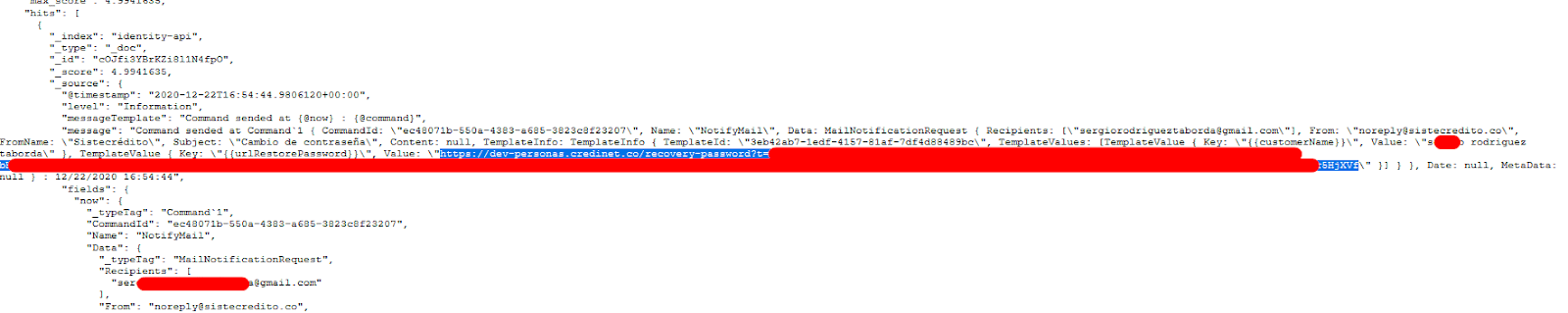
- Password reset links: Belonging to customers’ accounts.
Leaked information on the server that directly affects the Credinet platform includes:
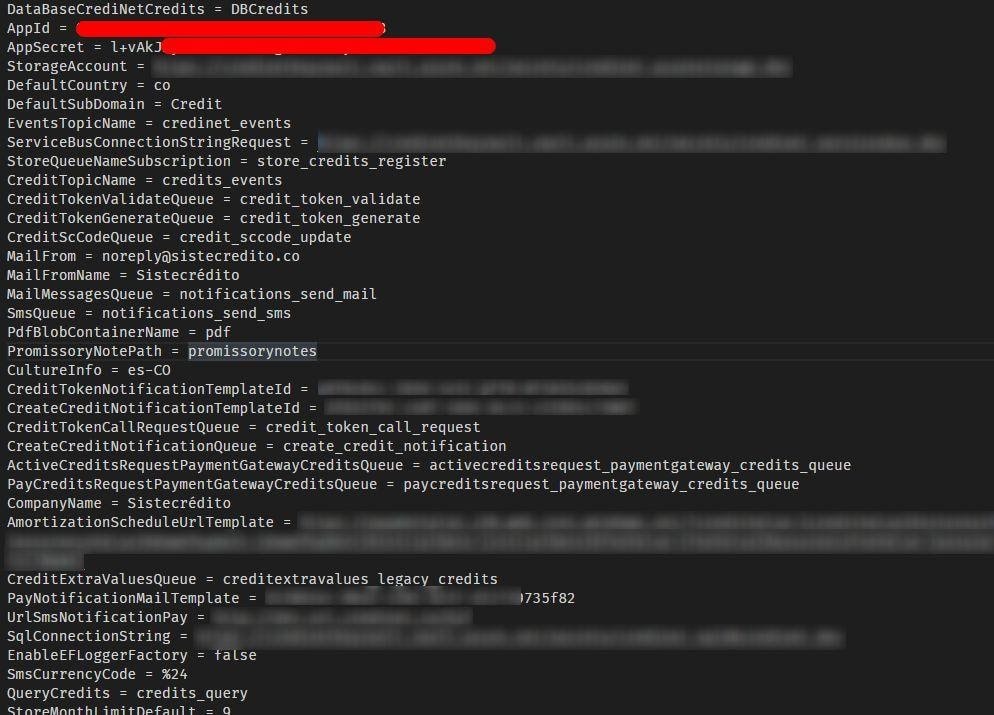
- Database credentials: Including cleartext passwords to the Credinet SQL database
- App secrets: One log contained various app secrets regarding the Credinet platform’s data storage.
Credinet/Sistecredito has exposed sensitive customer information that could be used to severely harm Credinet/Sistecredito and its customers.
Password reset links included in the database give us an idea of the impact of this breach. These could be used to provide hackers with access to thousands of user accounts.
A hacker could access the list of customer email addresses included in the database, using these details (along with reset links) to reset the password on the associated user account. As such, hackers could use these links to reset any one of the 3000 plus user accounts included in the Credinet database.
The prevalence of PII, reset links and JWT tokens poses the lowest estimated number of customers affected at slightly over 3000 users, though the figure is likely far greater.
Evidence of leaked JWT tokens, emails, password reset links, and other forms of PII can be seen below.
But Credinet/Sistecredito’s data leak may well affect the company’s own business directly, leading to a bigger leak of customer data in the future. This is because of two additional forms of data found on the server. One log contained ‘app secrets,’ which give further details about the platform’s data storage.
The research team also discovered 2 database passwords that would likely grant hackers additional access and privileges, including full control over the Credinet SQL database. Due to ethical reasons, our team did not test out these passwords.
Evidence of leaked ‘app secrets’ and database passwords can be seen below.

The inadequate security practices on the Credinet database mean the owners of the platform (Sistecredito) may come under the scrutiny of Colombia’s Superintendence of Industry and Commerce (SIC), which investigates any case of data misuse or poor data protection practice by Colombian enterprises.
If Credinet/Sistecredito is found to have misused customer data with criminal intentions, Credinet/Sistecredito will have broken the Colombian Criminal Code, which opens the case up to an alternative set of sanctions & punishments. Though, based on current evidence such an event seems unlikely.
Who was affected?
Sistecredito, along with its Credinet platform, is located in Colombia, and it’s not thought the company conducts any business outside of the Colombian border. An analysis of Credinet/Sistecredito’s company registration confirms it is located in Colombia, while Alexa traffic analysis shows that the company deals only with Colombian citizens.
Who Was Leaking the Data?
Sistecredito uses the Credinet platform to generate business and allow stores across Colombia to sign users up to its financing services.
Sistecredito is headquartered in the town of Envigado, located in the Antioquia Department of Colombia. Sistecredito is a large enterprise that currently employs around 300 people, with annual revenue of $15.78 million in sales (USD).
The content of the exposed database references Credinet/Sistecredito countless times throughout, and even contains links to the Sistecredito website and the Credinet platform. It’s therefore clear that the database belongs to Credinet/Sistecredito.
Impact on Credinet/Sistecredito Customers
Only Credinet/Sistecredito can know whether the database has been accessed by unethical hackers, however, the length of time it was open does posit users of the platform at significant risk of cybercrime.
Identity Theft & Fraud
Exposed PII from the leak, such as customer names, surnames, email addresses, mobile phone numbers, and financial data, could be used to assist in fraudulent activities across several other platforms. Cybercriminals could use this data to pose as the victim and commit fraud.
Scams, Phishing and Malware
Contact information, such as phone numbers and email addresses, could be used to target users with scams, phishing, and malware.
Hackers could use a customer’s personal information, including their financial records, to establish trust with the user, convincing them to hand over money, surrender additional PII, or click a link that downloads malicious software onto the customer’s computer.
Hackers could pose as a representative of Credinet or Sistecredito. Should the hacker contact users through email, they will likely try to coerce victims into clicking a link. This is a phishing attack. Once the victim clicks the link, malicious software could be downloaded onto the user’s computer – assisting hackers in further criminal activities.
Account Takeover
Password reset links and JWT tokens could be used to take over customer accounts.
Leaked JWT tokens can be used to authenticate oneself as a Credinet account holder. Hackers can also use password reset links to reset the password on any Credinet account.
The server’s leaked user list & email address list could be used to target victims with these attacks. Once hackers have accessed an account, they can see additional PII and can conduct other fraudulent activities.
Impact on Credinet/Sistecredito
Credinet, along with the owner of the platform, Sistecredito, looks as though it will incur several damages from this breach, both financially and reputationally.
Data Privacy Violations
The Superintendence of Industry and Commerce (SIC) is Colombia’s data protection authority, and will likely investigate the data practices of Credinet/Sistecredito.
Under Colombian law 1581, data controllers and processors must maintain strict security measures and standards concerning customer data. This prohibits the modification or disclosure of a customer’s data without their consent, whether intentional or not.
The SIC can issue fines of up to 2,000 times the Colombian minimum legal wage for perpetrators who break law 1581, along with Colombia’s wider data protection legislation.
The Colombian Criminal Code views any data violation as a serious crime if an entity exposes customer data on purpose, without authorization, to seek personal or third-party gain.
Any violation here could land the responsible individuals with a fine between 100 and 1,000 times the Colombian minimum legal wage, along with a prison sentence of 48 to 96 months. Though, there is currently no evidence that Credinet/Sistecredito exposed customer data on purpose.
In addition to these charges, affected users may even be entitled to receive compensation from Credinet/Sistecredito. Any legal pursuit of compensation could potentially wield results for affected parties, causing further financial harm to the company.
Loss of Business
The reputational damage incurred from such an event is tangible. Customers trust companies with their personal data, and when a company leaks this data an element of trust is broken.
Leaking data, whether intentional or not, infringes on a victim’s human rights. Credinet/Sistecredito has put customers at risk, which reflects poorly on the brand’s image.
Bad publicity may lead some consumers to avoid Credinet and Sistecredito in the future, while existing customers may terminate their relationship with the company if they feel unsafe, or are worried about the safety of their data.
Business Espionage
Credinet/Sistecredito is under serious risk of business espionage with so much customer data included on its open Elasticsearch server.
Rival companies could target the Credinet database’s customer list with offers, even tailoring their approach based on other forms of PII. This could take business away from the Credinet platform and Sistecredito’s financial services, as users migrate to its competitors.
Competitors could even pose as a colleague to Credinet or Sistecredito employees. A representative from a rival business could build trust with Credinet/Sistecredito employees by referencing customer accounts/information.
Eventually, the representative may ask questions about the business operations of Credinet and Sistecredito in the hope of revealing industry secrets.
Database Credentials
Leaked database credentials, like app secrets and database passwords, could be used to elevate privileges and expose further sensitive information.
While the database was already left in open form, database passwords would likely allow hackers to gain full control of the database. Especially if it doesn’t have extensive security features beyond database name and password authentication.
The passwords may grant hackers access to the server from various IP addresses that were previously blocked, which could put the Credinet SQL database at risk too.
Meanwhile, app secrets could allow hackers to identify where Credinet/Sistecredito’s confidential data is stored, potentially increasing the severity of an exposure’s impact.
Status of the Data Breach
Discovering the owner of the database was fairly straightforward, given the extensive references and website links to Credinet and Sistecredito throughout the content of the database.
We discovered the open Elasticsearch server on December 31st, 2020. After finding the database, we sent responsible disclosure of the data breach to Sistecredito on January 3rd, 2021, for which we never received a reply.
On January 11th, 2021, we contacted the Colombian CERT (Computer Emergency Response Team). The CERT team replied on January 17th, 2021. However, before disclosing the breach to them on January 18th, 2021, we checked the Elasticsearch and, fortunately, we found that the server was unreachable, and therefore seems to have been taken down. Although we found the server was secured on January 18th, 2021, it’s possible that the breach was closed before this date.
We’re not certain whether the breach was closed at the request of Colombian CERT or not, as Colombian CERT didn’t respond to our message before the breach was closed.
We must also mention that the unsecured server showed users that have recently received credit through Credinet/Sistecredito. This suggests that the server was still live and being updated regularly at the time it was unsecured.
Protecting Your Data
If you’re a customer of Sistecredito that has used the Credinet platform, or a representative of the business, there are some steps you can take to minimize the impact of any potential cybercrime.
First of all, fearful customers are entitled to request that the company updates, modifies or deletes their personal data. Companies must comply with Colombia’s data protection laws.
To avoid scams, phishing attempts, and malware, users should be extra vigilant when interacting with unknown parties over the phone or through email. Especially parties who claim to be a representative of Credinet, Sistecredito, or the bank. Request proof that the person is who they say they are, and avoid clicking a link unless you are absolutely sure the party is trustworthy.
Financial statements and the activity of users’ bank accounts should be monitored continuously. Although not much can be done about account takeover in this scenario, users should alter account information where they can.
As for Credinet and Sistecredito, employees should be aware of any individuals attempting to pose as a colleague or illegitimate customer. Put authentication procedures in place for colleagues, and be wary of anyone asking too many questions about business operations.
Credinet/Sistecredito should change any database credentials that have been leaked in the breach, such as the location of app secrets and server passwords.
How and Why We Report on Data Breaches
We want to help our readers stay safe when using any website or online product.
Unfortunately, most data breaches are never discovered or reported by the companies responsible. So, we decided to do the work and find the vulnerabilities putting people at risk.
We follow the principles of ethical hacking and stay within the law. We only investigate open, unprotected databases that we find randomly, and we never target specific companies.
By reporting these leaks, we hope to make the internet safer for everyone.
What is Website Planet?
Website Planet prioritizes honesty and serves as the premier resource for web designers, digital marketers, developers, and businesses with an online presence. We provide tools and resources catering to individuals at every skill level, from beginners to experts.
We have an experienced team of ethical security research experts who uncover and disclose serious data leaks as part of a free service for the online community at large. This has included a breach in a famous european office supplier, as well as a breach in a Indian B2B online packaging marketplace leaking sensitive data.
You can read about how we tested five popular web hosts to see how easily hackable they are here.