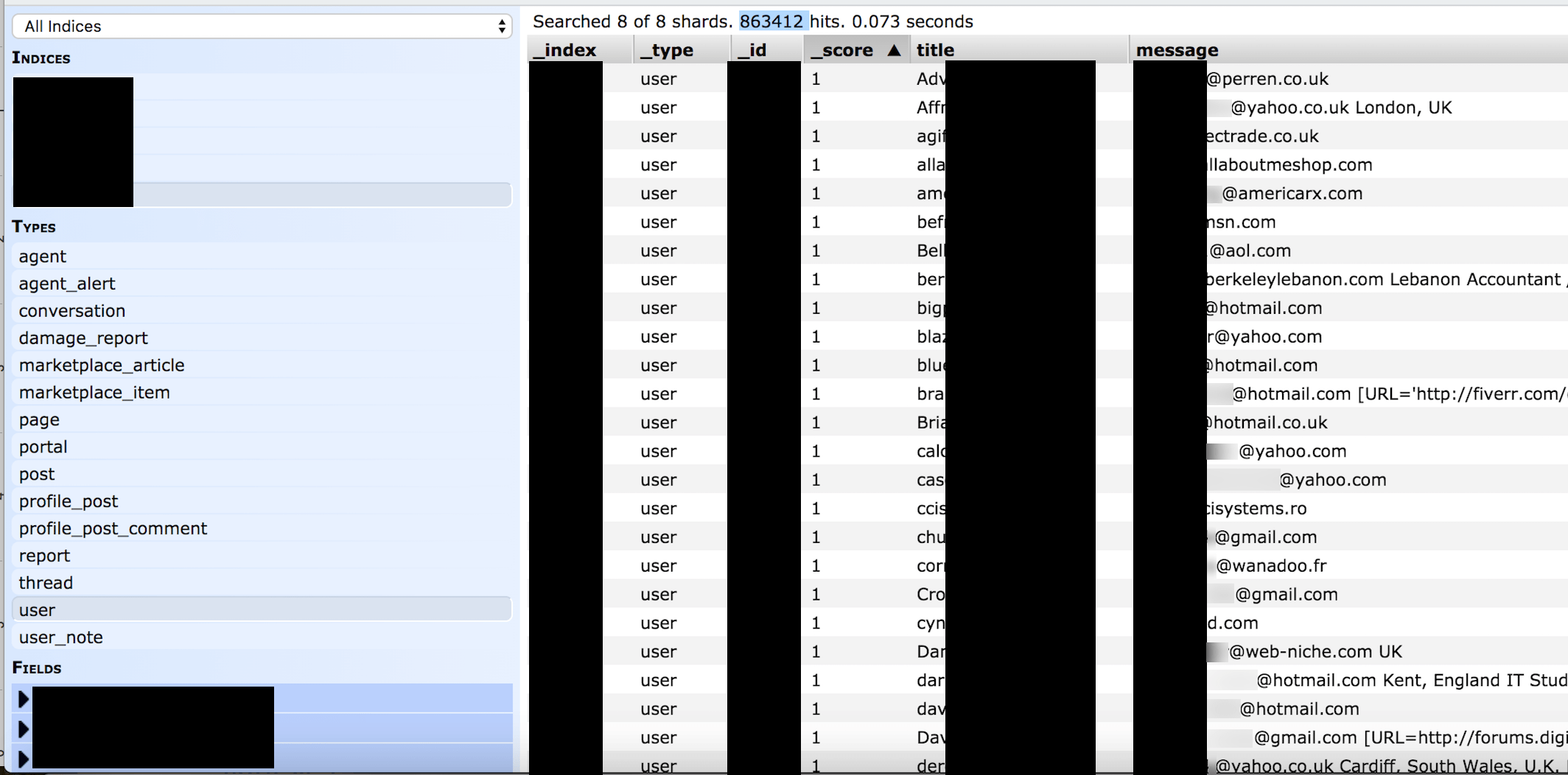
Another day and another big data leak. On July 1st the WebsitePlanet research team in cooperation with Security Researcher Jeremiah Fowler discovered a non-password protected database that contained records of the internet’s largest webmaster portal. Upon further research it appeared that Digital Point had leaked the data of 863,412 users.
Digital Point claims to be the world’s biggest webmaster forum and marketplace for web related services. The forum lets people buy and sell websites, SEO, and a wide range of services. The site caters to those individuals who maintain or create websites either for themselves or customers.
Data Breach Summary
| Domain | DigitalPoint.com |
| Location | San Diego, California |
| Industry | Internet Forum / Webmaster |
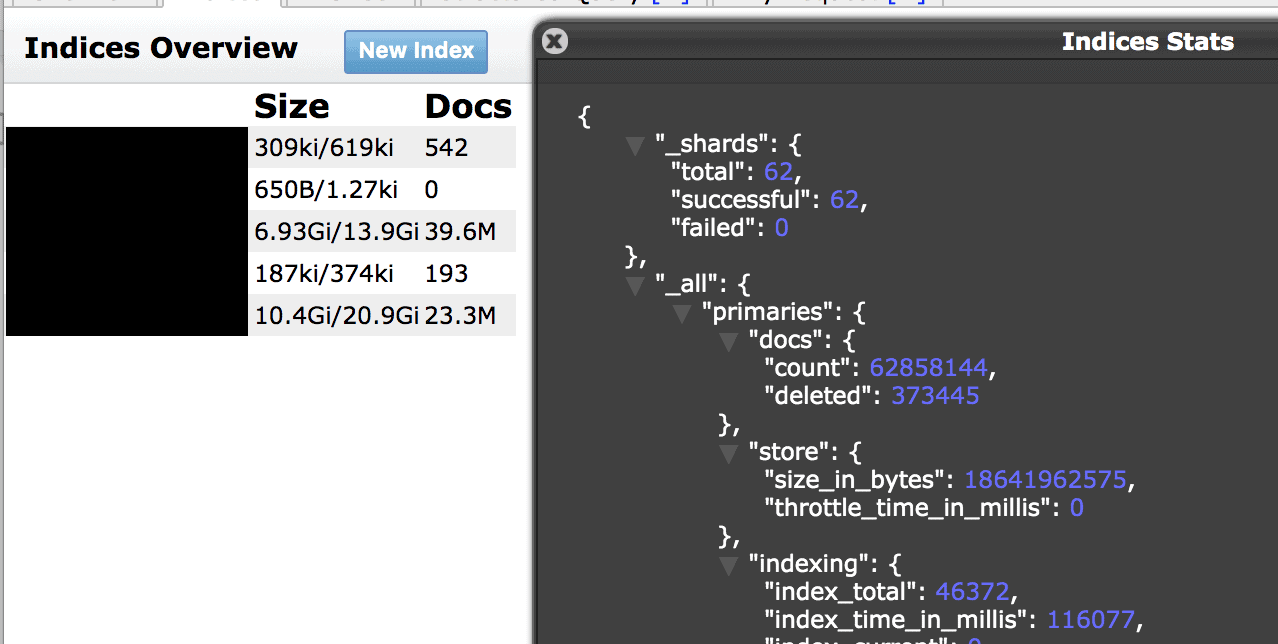
| Total number of Records | 62,858,144 records |
| No. of people exposed | 863,412 Digital Point Users |
| Geographical scope | Worldwide |
| Types of data exposed | User emails, names, internal user ID numbers, Internal records and user posts. |
| Potential impact | Domain Hijacking, targeted phishing attempts, email based malware attacks, social engineering. Database at risk for ransomware. Middleware information that could allow for a secondary path for malware. Storage info that cyber criminals could exploit to access deeper into the network. |
| Data storage format | This is an Elastic database set to open and be visible in any browser (publicly accessible) and could have been edited, downloaded, or even deleted data without administrative credentials.
*As Security Researchers we never extract data or circumvent password or other security measures. We only take a limited number of screenshots to validate our discoveries. |
According to their LinkedIn Profile “Digital Point is the internet’s biggest webmaster forum. Thousands of freelancers earn their lives with Digital Point forums. There are freelancers, service providers, coders, marketers and people from almost every profession here”
This data exposure raises the risks of a targeted phishing campaign and domain hijacking. Having the contact information, email and other details could allow a cyber criminal to use acquired personal information about the actual domain owner to impersonate them. Domain hijacking is exactly what it sounds like and criminals could try to change the registration information and ownership details. This type of theft would allow the domain hijacker to gain full control of the website name and can use the domain for their own purposes or try to sell it to a third party. Every bit of data is a puzzle piece that can be used to create a full picture or profile of the person or target. The exposed database contained user posts and activity, so in theory this would have identified users who were selling domains, their value or asking price etc.
I am not implying that Digital Point’s users are at risk of this type of phishing, but only raising awareness to the real threat of domain hijacking. This dataset would have been a treasure chest of information for domain hijackers. Many of the email accounts were admin@ or similar. Having a domain stolen can destroy a business or an organization and there is no guarantee that you will get it returned. Anyone who has ever lost a domain name will tell you that dealing with lawyers, court costs, and losing the trust of your clients would be devastating.
There are steps that webmasters can take to try and protect their domains. One of the easiest ways is to enable two-factor authentication. Use a strong password, change it periodically, and never reuse passwords for multiple accounts. This may seem like common sense, but as humans we get comfortable and mistakes happen. One last step is never provide your admin credentials to anyone unless you can validate or verify who the person is and that they have a real reason to request that information.
The internal records also gave a look inside how the forum is operated, the type of data Digital Point collects and stores. One interesting collection included users and forum members who reported or flagged posts and why. They wrote detailed descriptions of why they were telling on someone and what they didn’t like. Some were legitimate about bad business dealings or spam while others seemed petty and personal. Obviously, users who anonymously report their fellow members would not want that publicly exposed.
The database was also at risk of ransomware and luckily discovered and secured just two weeks before the “Meow Bot” wiped out thousands of databases around the world virtually overnight. One of the dangers of a non-password protected database is that it is a sitting target waiting to be stolen, encrypted, or deleted. Not only was there a potential risk to users who may be targeted via their contact information, but the entire network was exposed and vulnerable to attack.
Digital Point’s Backstory and Founder
I had heard of them before but was unaware that Digital Point had such a colorful history until conducting additional research for who to send the data exposure notice to. Digital Point was founded in the early 2000’s by Shawn Hogan who went from a software and SEO guy to one of the most notorious affiliate marketers of the time. In 2011 Ebay sued Digital Point claiming Hogan had defrauded eBay of an alleged $28 million in online marketing fees.
According to an article in Business Insider “Hogan had become the No. 1 affiliate marketer at eBay out of an army of 26,000 others. He was also ranked No. 2 among Google’s AdSense partners in 2013”.
eBay secretly worked with the FBI and had monitored the traffic he was sending since 2006. He was doing so well with making affiliate commissions that they began to suspect that the web traffic was somehow rigging eBay’s system and rewarding Hogan in the process. The FBI and eBay claimed that he managed to do this by planting cookies so that the affiliate network would pay a commission. Hogan claimed that no wrongdoing and that eBay’s affiliate team encouraged him to keep up the good work. In the end Shawn Hogan, was sentenced to five months in federal prison and given three years on probation, and fined $25,000.
As soon as we discovered the database on July 1st, we promptly issued a responsible disclosure notice regarding the data incident. Within hours of the notification, we restricted public access to the data. Despite this, we did not receive any response from Digital Point to the initial data exposure notice or the subsequent follow-up request. At the time of this publication, no comment or reply from Digital Point has been received.