Researchers See Russian Databases Targeted With Files Erased and Folders Renamed With Pro Ukrainian Messages.
Together with the Website Planet research team we took an indepth look at the cyberattacks targeting Russian websites, technology and cyber assets, perpetrated by the famous group, Anonymous. On the same day of Russia’s unprovoked attack against Ukraine, a Twitter account associated with the “Anonymous” hacking collective called on hackers from around the globe to target Russia and it appears that hackers are answering the call.
For the record; I am an American citizen who has lived and worked in Ukraine for nearly a decade. In the early morning hours of February 24th the Russian invasion of Ukraine began. I packed up a few belongings, computers, hard drives, and personal items and fled the city of Kyiv as fast as possible. By 7am there were already hours long lines to gas stations and major roadways were nearly stopped with traffic. It took 4 agonizing days to get to the Polish border where over 115,000+ Ukrainians had crossed in just the first 3 days alone.
Now temporarily based in Krakow, Poland and back online, I started searching to see what activity was happening online and what Russian information had been exposed following Anonymous’ call. As ethical security researchers, we are always looking for exposed data and information and never target any specific organization or geographic location. In our research for this report we were looking for publicly exposed data that was hosted on IPs located in the Russian Federation and using non-password protected cloud storage repositories, to understand what were the “cyber impacts” of the “real world events”. For the last few years pro-Russia hackers had been targeting Ukraine, and since Anonymous’ call we could see a turnaround in cyber activity now targeting Russia that we wanted to look closer into.
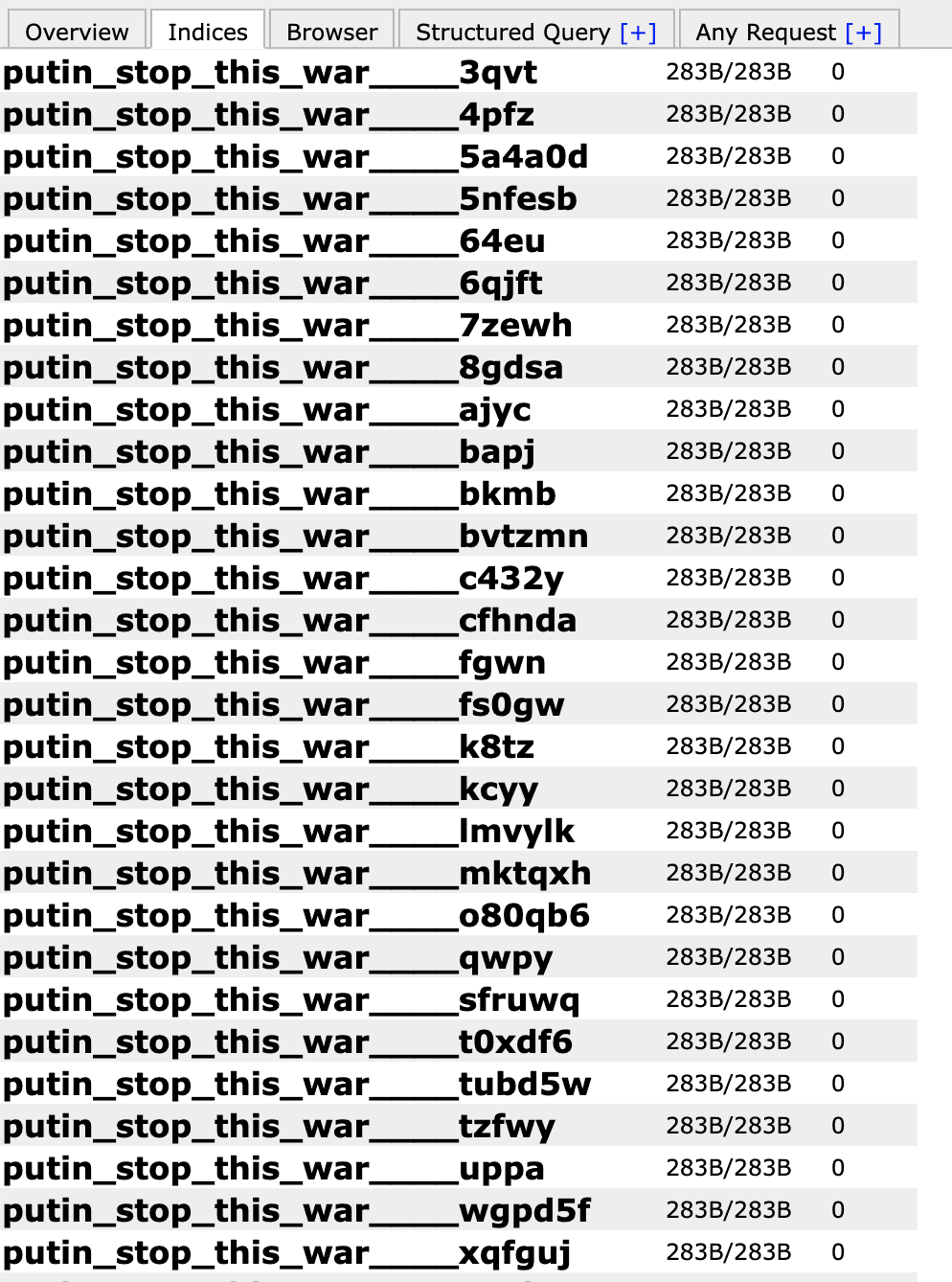
The most recurring event we saw were multiple data sets where the file names were changed to “Glory to Ukraine” (Слава Україні) – a reference to Ukraine’s battle for independence in 1918-1920. It was also the rallying cry of the “Revolution of Dignity” in 2014 that overthrew the Russian backed president Viktor Yanukovych and took Ukraine further away from Moscow. It was clear that hackers had accessed these databases, deleted files, and launched a cyber vandalism campaign leaving folders with names like: “putin stop this war”, “stop war”, “no war”, “HackedByUkraine”, and many other pro Ukrainian messages.
It appears that for the majority of the databases we reviewed, most of the files in the folders were wiped out and no longer appeared in the dataset. The anti-Russian hackers used a similar script to the infamous “MeowBot” that changed the name of folders and deleted the contents of the files. In August 2020 Security Discovery’s Bob Diachenko profiled the Meowbot attack that erased thousands of databases over the span of a few days and caused havoc on victims who lost their data and had no way to get it back. Unlike ransomware that encrypts data and demands a payment the MeowBot had no demands. The automated script seemed to have no other purpose except to wipe out data. Some of the activity in the Russian databases appears to be very similar to the 2020 MeowBot attacks (except that this time the demand is for the war to stop).
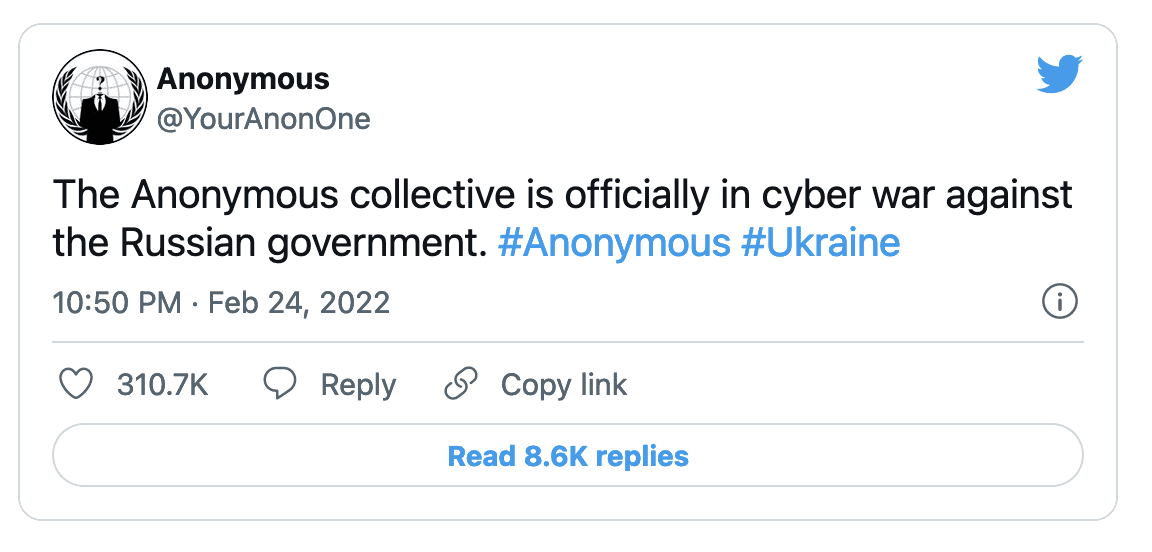
Since the start of the conflict members of Anonymous and other groups have targeted Russian state media outlets, government websites, and what appears to be any Russian and Belarussian database that was already exposed or newly misconfigured datasets.
This is an example of how a single cause can unite a global network of individuals outside of any government control. Reports claim that Anonymous has disrupted websites of the oil giant Gazprom, the state sponsored news channel RT (Russia Today) and shut down the Control Center of the Russian Space Agency ‘Roscosmos’. On March 7th 2022, Anonymous claimed to hack Russian state TV stations Russia 24, Channel One, and Moscow 24 to air footage of the war in Ukraine which many Russian citizens are unaware of. In addition to hacking there have been significant denial-of-service (DDOS) attacks where the website’s server is overwhelmed with traffic and unable to function. These attacks are often distributed among so many machines, devices, and IP addresses that they are nearly impossible to defend against.
In a random sampling of 100 Russian Databases 92 had been compromised.
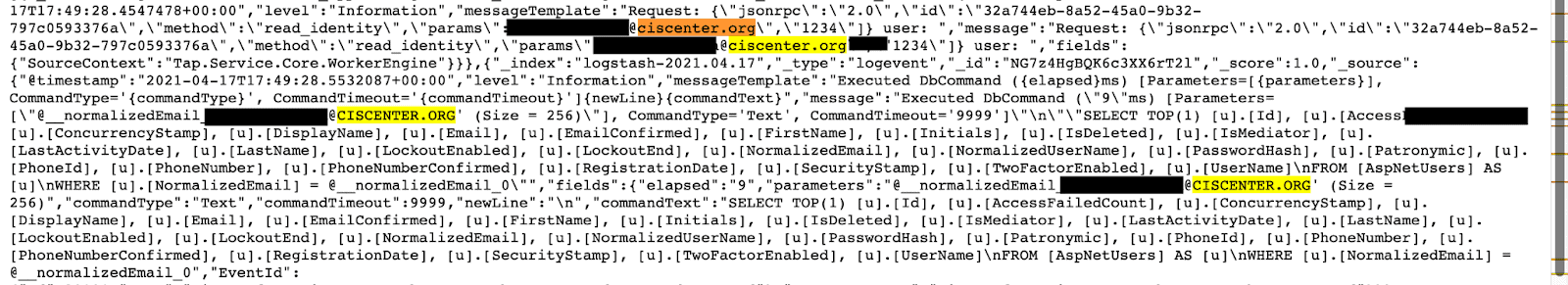
One of the databases we discovered that had been accessed by hackers belonged to ciscenter.org. The Commonwealth of Independent States (CIS) was established at the end of 1991, after the fall of the Soviet Union and includes Russia and 11 other republics. The CIS Center is an organization that coordinates information and regulatory practices on trade, finance, lawmaking, and security between CIS Member States. Hundreds of folders in the database had been renamed to “putin_stop_this_war”. In addition to the hack it appears that the database exposed very weak administrative credentials and numerous emails. This would also make employees easy targets for social engineering to gain access deeper in the organization or social engineering.
Often when data is exposed it is unknown if the information was compromised and only a detailed forensic analysis (by the owner) can uncover unauthorized access. However, in this case we know for a fact that hackers found and probably accessed these systems. We do not know if data was downloaded or what the hackers plan to do with this information, but most chances these exposed individuals face real risks of further cyber actions.
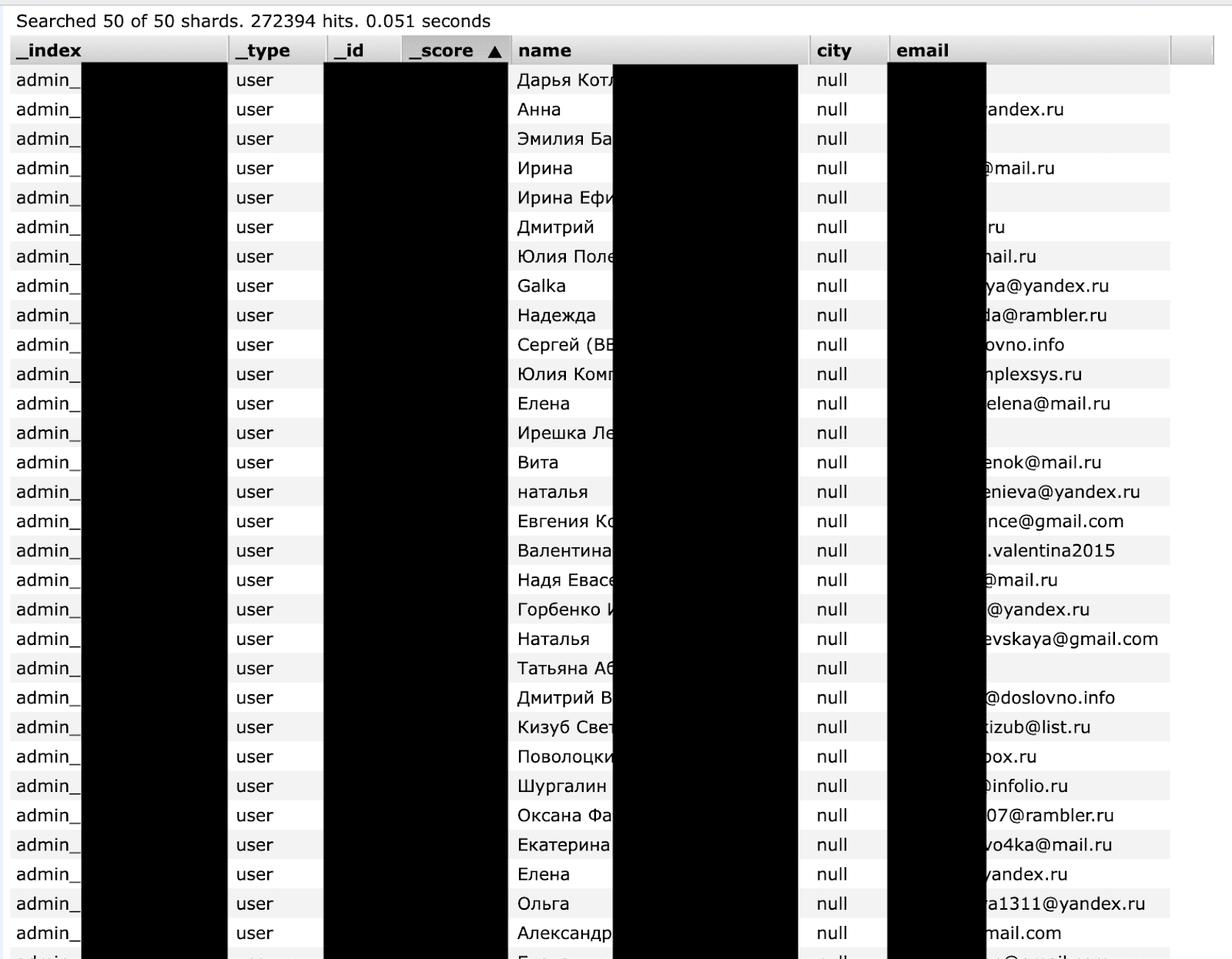
Not all files were deleted from every database and some contained personally identifiable information. One at risk database contained information on 272,394 individuals listed as “users”. We were unable to identify the owner of this database, but it also contained pro-Ukrainian messages. The records included email addresses, names, internal IDs, and administrative information. Knowing the names and email accounts of these individuals could allow members of Anonymous and others to target them in spear phishing campaigns or send malware directly to the target in an attempt to infect their devices.
We used multiple sources to find these misconfigured databases including IoT engines. The same methods legitimate security researchers use to find data can also be used by hackers. These datasets have been found by activist hackers (or “hacktivists”) and we can only assume they are affiliated with or supporters of Anonymous based on the timeline of when the Russian databases were targeted.
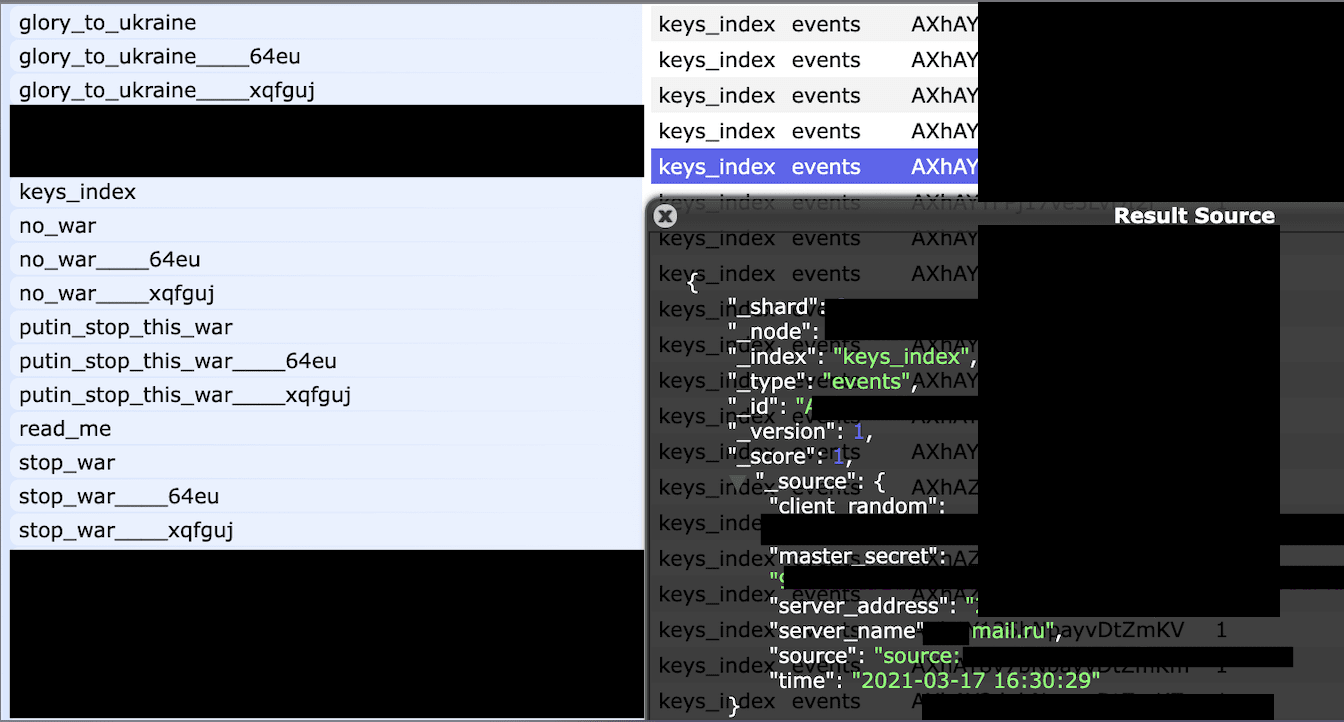
Among the sampling of cloud storage databases we discovered a very large number of secret keys and referenced mail.ru, one of the biggest email providers in Russia as the host server. The danger of exposing a private or secret key is that it can be used to unlock or decrypt encrypted information and expose any sensitive data or information in the same way a physical key unlocks a door. The database also included messages and folders indicating it had been targeted by hackers. It is unclear if the keys have already been used or what data they could reveal.
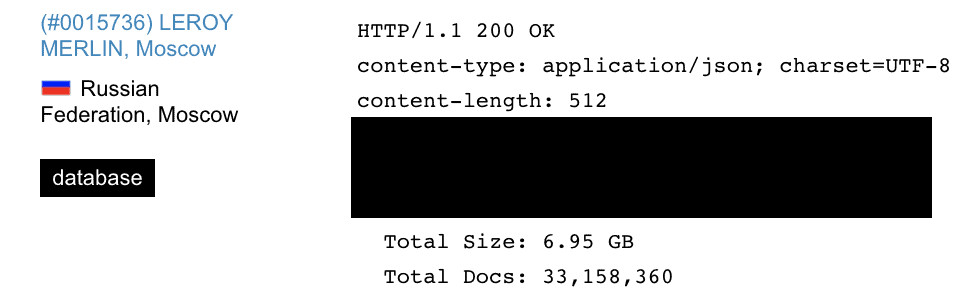
Other notable exposed datasets we found during our research included the Russian Internet provider “Green Dot” (Зелёная точка) that provides internet and digital TV service in 18 cities throughout Russia and contained 2.2 million records. There were a small number of files renamed but not deleted as in other databases. We believe this could be due to the permission settings on the individual databases. Theoretically, hackers would have enough internal information to try and disrupt the service or target other areas of the network. We also discovered a Russian-based dataset containing information belonging to the French home improvement and gardening retailer Leroy Merlin. This database contained analytics, security, authorization logging data, admin credentials and internal passwords. Like the others there were files renamed to pro-Ukrainian messages.
***We attempted to notify the affected or at risk organizations and when we couldn’t identify the owner we reached out to the hosting provider in attempts to protect and secure the exposed data.
Anonymous has a history of cyber activism
Founded in 2003 Anonymous claims their purpose is anti-cyber-surveillance, anti-cyber-censorship, internet activism, and internet vigilantism. In the past Anonymous has targeted government agencies of the United States, Israel, Tunisia, Uganda, and others. The group has also gone after corporations such as PayPal, MasterCard, Visa, and Sony just to name a few. There are several affiliated groups such as LulzSec, AntiSec, NB65, and many others. It is believed that many of the Anonymous members are involved in multiple campaigns based on issues or causes they individually support. Since 2009 only a small number of Anonymous members have been arrested or gone to trial for hacking or other cyber crimes.
Russian internet censorship leaves very little room for opposition inside of the country, but Russians living outside of the country have voiced their discontent with the attack on Ukraine. A cyber attack is one way for an informal collective such as Anonymous to make a big impact or create major disruptions no matter where they are located in the world, while limiting the repercussions (whether legal or “physical”). Russian speaking hackers could be a valuable asset to any group taking aim at Russian cyber assets by providing insider knowledge and navigating the language. What makes these cyber attacks even more complex to defend against is that they can not be connected to any state, country, or specific group. Anonymous has proven to be a very capable group that has penetrated some high value targets, records and databases in the Russian Federation.
Once hackers succeeded in compromising Russian websites, servers, and networks, Russian authorities alleged that the attacks originated from the United States. However, it is highly improbable that this assertion is accurate, given the global presence of Anonymous members and their capability to utilize a VPN (virtual private network) to effectively conceal a user’s location and internet traffic.
Cyber Warfare is the New Normal
When we think of war we imagine tanks, rockets, and boots on the ground. There is now a new modern component in the form of a coordinated cyber attack and it has been going on in the digital shadows for years. Cyber warfare is attacking a nation’s critical infrastructure, computers or information networks, and disrupting the free flow of information or communication. While Russia seems to use their cyber weapons more often, other countries have also developed tools for cyber warfare. These include the United States, China, the UK, Australia, Canada, France and Israel. The methods we see being used today give a glimpse into the future of how wars will be fought using technology in addition to bombs.
The Russian cyberweapon called “Uroburos” has been around since 2005. The word Uroburos is a circular symbol depicting a snake or a dragon swallowing its tail and represents the idea of infinity or a reference to a never ending cyber attack. Days before the Russian attack on Ukraine the country was targeted with a new type of malware called “HermeticWiper”. This basically destroyed devices by preventing computers from rebooting. It appears to target only devices with Ukrainian language keyboards. This is a common practice and it was identified that many previous malware and ransomware instances would not fully engage if the device was set to a Russian language keyboard. We can only speculate it is not likely that this was a coincidence.
Russia is suspected of first launching cyber attacks on Ukraine’s public and private information systems in 2013 and disabled Ukraine’s power grid on Christmas 2015 and again 2016. Other events include the State Treasury of Ukraine in December 2016, supply-chain attack in June 2017 and attacks on Ukrainian government websites in January 2022.
The compromised Russian datasets we saw were from a wide range of organizations and companies and we only highlight our findings for security awareness and educational purposes.
As a security researcher I never circumvent passwords or use credential information to access password protected assets. We look for publicly exposed data and see what is inside those specific databases to understand what information they contain, who is affected, and what are the real world security risks. We never modify, delete, or have any interaction with the data other than reading what the files contain. It is important to highlight that our research was only for reporting purposes and we didn’t take any action in any cyberwarfare (now or at any other time) and despite my personal background, I did not take any action online that does not follow the rules of ethical hacking.